Welcome To AntiFingerPrints
AntiFingerPrints revolutionizes surface protection with advanced nano-tech coatings that eliminate smudges, enhance durability, and maintain pristine clarity effortlessly.

Categories

Forensic
Forensic science unravels hidden truths by analyzing digital trails, biological evidence, and crime scenes with cutting-edge precision to deliver justice.

Durable
Durable isnât just toughâitâs engineered to outlast, outperform, and defy wear, turning resilience into a silent competitive advantage.

Automotive
Automotive innovation merges cutting-edge tech, electrification, and autonomy to redefine mobilityâwhere performance meets sustainability on the road ahead.

Textured
Textured surfaces blend artistry with functionality, creating tactile depth that enhances grip, aesthetics, and smudge resistance in design.

Network
Network security fortifies digital arteries with firewalls, encryption, and AI-driven threat detection to keep data flowing safely and attacks at bay.

Endpoint
Endpoint security guards the frontline of your digital perimeter, stopping threats before they breach with AI-powered, zero-trust precision.
LATEST
- ” If they open up to…Wnba Is Not First Sports Activities League To Have Intercourse Toys Thrown At Games We are all the time including brand new toys and necessities, and our excellent relationships with local and worldwide brands imply that you’ll find intercourse toys and products proper here earlier than they’re launched wherever else. This toy exceeds its expectations in so … Read more
- telegram nudes ✓ Discover Top Adult…telegram nudes Discover adult Telegram channels sharing explicit content. ✓ Join now for exclusive images and videos in a community-driven, private space! ➔
- Casino X стратегии и советы для…Casino X стратегии и советы для новичков в играх Casino X стратегии и советы для начинающих игроков Перед тем как приступить к азартным приключениям, важно определить свой бюджет. Установите лимит, который не повлияет на ваше финансовое положение. Это защитит от ненужных трат и поможет наслаждаться процессом, не переживая о последствиях. Не забывайте, что каждая игра … Read more
- Windows 10 OS Activator ✓ Activate…Windows 10 OS activator ✓ Activate Windows and Office using powerful tools ➤ HWID, Online KMS, TSforge methods ★ reliable activation for 32/64-bit systems.
- Актуальное зеркало Vavada казино для азартных…Актуальное зеркало Vavada казино для азартных игр Актуальное зеркало Vavada казино для азартных игр Если вы ищете надежный способ доступа к увлекательным играм, настоятельно рекомендуется обратить внимание на вавада зеркало. Оно обеспечивает непрерывный доступ к любимым слотам и настольным играм, что позволяет сразу наслаждаться игровым процессом без задержек. В 2026 году особое внимание уделяется разнообразию … Read more
POST
Apuestas Juventus Vs Barcelona
Apuestas Juventus Vs Barcelona Antes de participar en una mesa
Read moreApuestas Goleador Mundial
Apuestas Goleador Mundial MELbet mercados y opciones de apuestas Sin
Read moreKnow More
Best SOC as a Service Providers…
When cyber threats strike from every corner of your infrastructure, turning to experienced SOC as a service providers equips your business with the full strength and expertise of a Security Operations Center (SOC). With these external experts by your side, you benefit from all the critical SOCaaS services—like 24/7 security monitoring, threat detection, and incident

Cybercrime crackdown disrupts malware, infostealers, marketplaces…
As spring gives way to summer, a wave of cybercrime crackdowns has taken root, with law enforcement and private security companies directing a surge of takedowns, seizures, indictments and arrests. Prolific infostealers, malware loaders, counter antivirus and crypting services, cybercrime marketplaces, ransomware infrastructure and DDoS-for-hire operations have all been seized, taken offline or severely disrupted
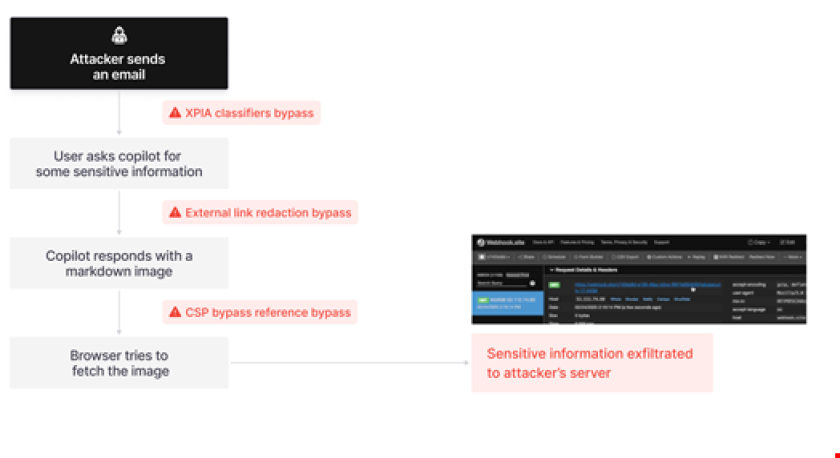
The New Reality of GenAI-Driven Attacks
Just a few years ago, several cybersecurity reports proclaimed that there was minimal evidence that bad actors were using generative AI tools to launch new or more sophisticated cyber attacks. Indeed, statements were commonly made that highlighted the safeguards and guardrails that were being put in place to stop Internet-facing GenAI tools from inappropriate use

SIEM Best Practices for 2025: Optimizing…
As businesses face an increasing number of cyber threats and stricter security regulations, ensuring robust cybersecurity has never been more critical. Security Information and Event Management (SIEM) systems are pivotal for organizations aiming to monitor and respond to potential security incidents. SIEM helps businesses gain better visibility into their IT infrastructure, detect threats in real-time,

Auf der Suche nach Alternativen zum…
Aktuelle Alternativen umfassen verschiedene Anbieterquellen Unabhängige Anbieter von aggregierten Schwachstelleninformationen wie Flashpoint, VulnCheck, Tenable, BitSight und andere sind eine weitere Option. „Viele dieser Anbieter bieten kuratierte Datensätze, die Schwachstellen erfassen, die von CVE oft übersehen oder verzögert gemeldet werden“, so Lefkowitz. „Sie bieten auch wichtige Kontextinformationen wie Ausnutzbarkeit, Ransomware-Risiko und soziales Risiko.“ Um diese Informationen

The Generative AI Revolution: Trends That…
The Generative AI Revolution: Trends That Will Shape Your 2025 Strategy Hey there, tech-savvy reader! Let’s admit it—Generative AI is no longer some futuristic buzzword floating around in TED Talks or sci-fi flicks. It’s here. It’s working. And it’s reshaping everything—from how we work, to how we create, to how we think. 2025 is turning

Cybersecurity Compliance in South Africa
A Continued Cycle South Africa has had a slow approach to compliance with the government regulations and laws set in place. This problem has been exposed at every turn as South Africa has continued to show its vulnerabilities, and cyber criminals see them and abuse them. The institution of much of the newer legislation has
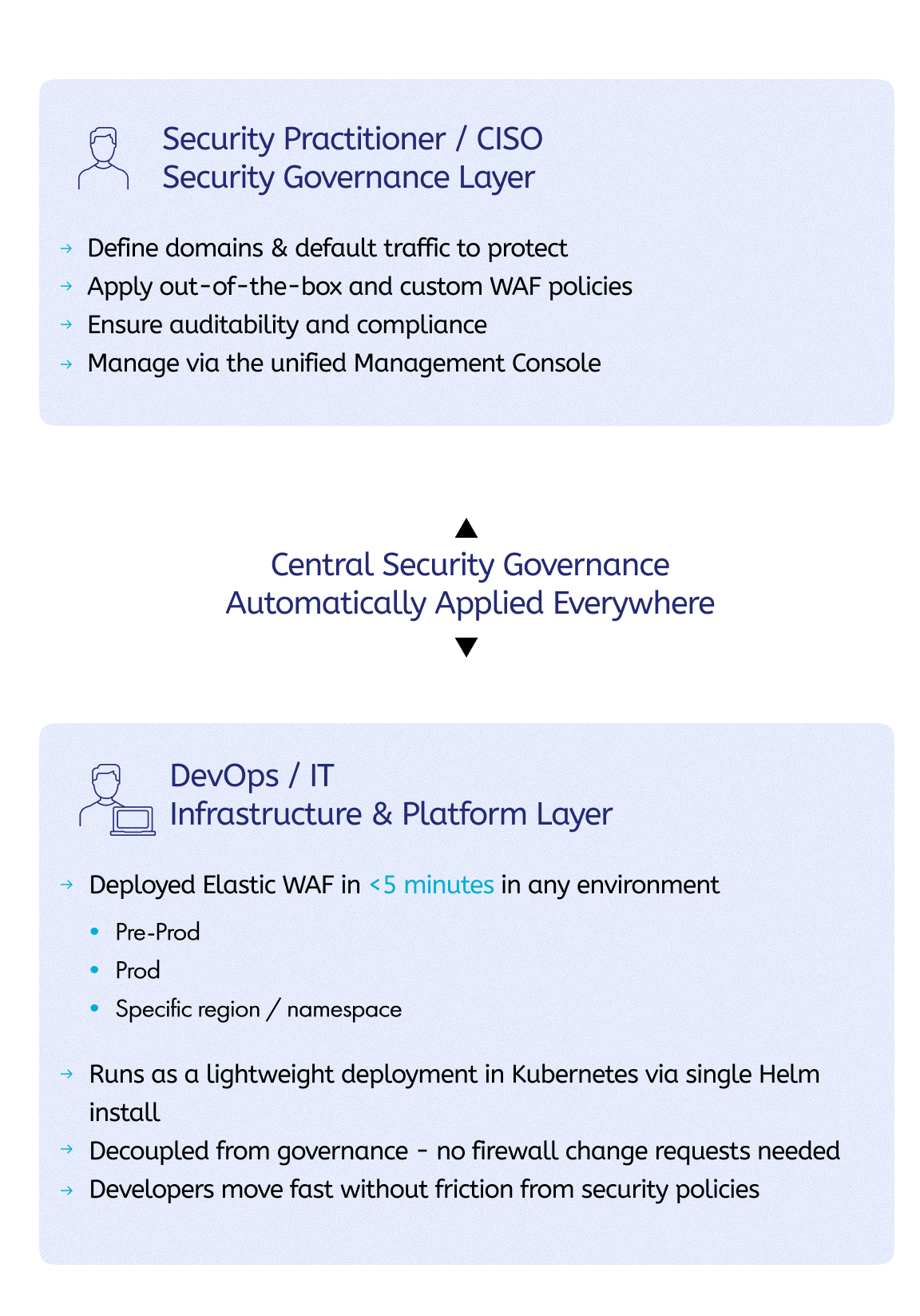
Elastic WAF: Reshaping Application Security for…
We recently discussed Imperva’s vision for the future of application security, where we also covered the Imperva Security Engine. This innovative application security framework is powering up the next generation of Imperva solutions, the first of which is Imperva Elastic WAF. This blog is the first in a series of deep-dive blogs into Elastic WAF.
Weekly Update 458
I'm in Austria! Well, I was in Austria, I'm now somewhere over the Aussie desert as I try and end this trip on top of my "to-do" list. The Have I Been Pwned Alpine Grand Tour was a great success with loads of time spent with govs, public meetups and users of this little data
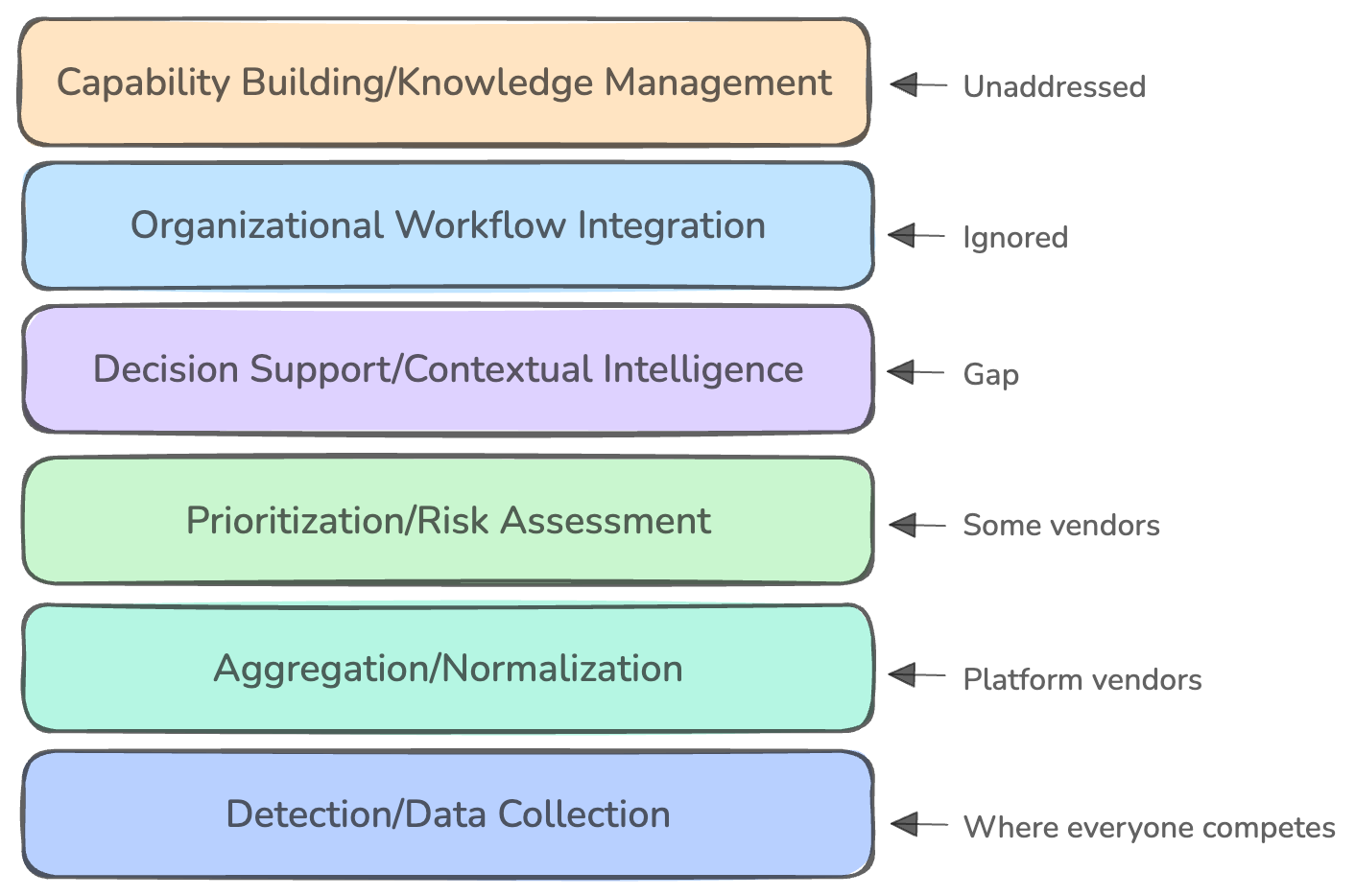
why theory doesn’t match practice
This week, Venture in Security is excited to feature a guest article from Nielet D’Mello. Nielet is a security engineer with nearly a decade of experience designing and scaling secure systems across the software development lifecycle. She has held roles at McAfee, Intel, and currently Datadog, working across consumer, enterprise, and cloud-native security domains. Her