Digital Identities: Getting to Know the...
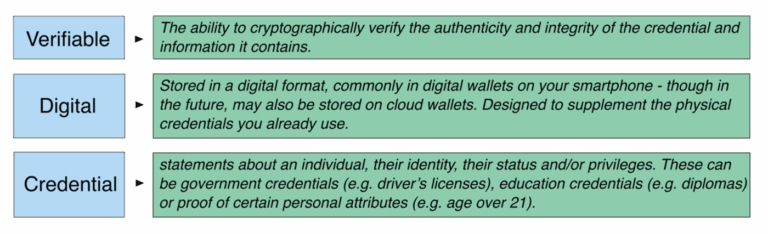
If you are interested in the world of digital identities,
Read more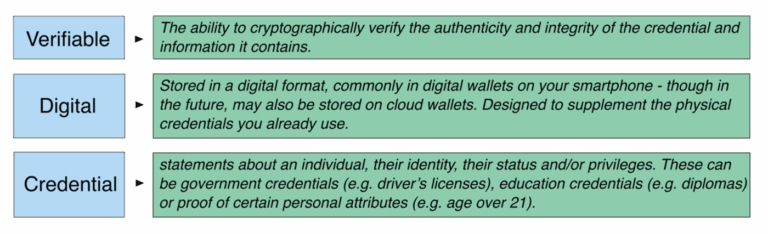
If you are interested in the world of digital identities,
Read more
This episode of Coffee with the Council is brought
Read more
Posted by Il-Sung Lee, Group Product Manager, Android Security Protecting
Read more
Key Components of an Incident Response Plan A robust incident
Read more
Hello CyberBuilders 🖖 Let’s talk AI security (don’t stop reading
Read more
Layered Security – How a Defense-in-Depth Approach Guards Against Unknown
Read more
WhatsApp US House bans WhatsApp from 12,000+ staff devices over
Read more
Managed security services providers, or MSSP providers for short, have
Read more
The Forminator plugin for WordPress is vulnerable to an unauthenticated
Read more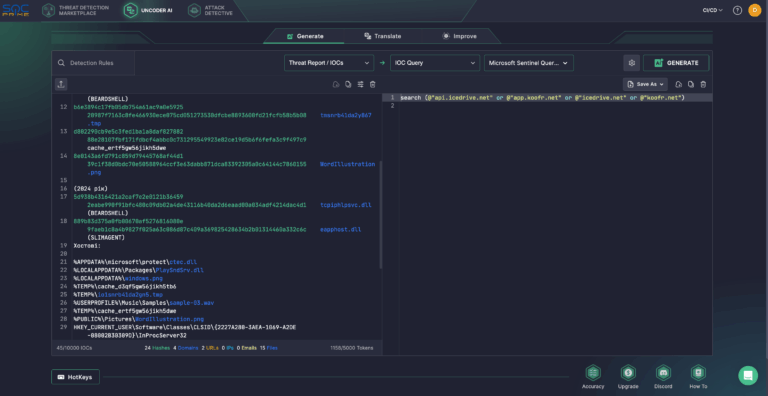
The nefarious nation-backed russian hacking collective known as UAC-0001 (aka
Read more