Welcome To AntiFingerPrints
AntiFingerPrints revolutionizes surface protection with advanced nano-tech coatings that eliminate smudges, enhance durability, and maintain pristine clarity effortlessly.

Categories

Forensic
Forensic science unravels hidden truths by analyzing digital trails, biological evidence, and crime scenes with cutting-edge precision to deliver justice.

Durable
Durable isnât just toughâitâs engineered to outlast, outperform, and defy wear, turning resilience into a silent competitive advantage.

Automotive
Automotive innovation merges cutting-edge tech, electrification, and autonomy to redefine mobilityâwhere performance meets sustainability on the road ahead.

Textured
Textured surfaces blend artistry with functionality, creating tactile depth that enhances grip, aesthetics, and smudge resistance in design.

Network
Network security fortifies digital arteries with firewalls, encryption, and AI-driven threat detection to keep data flowing safely and attacks at bay.

Endpoint
Endpoint security guards the frontline of your digital perimeter, stopping threats before they breach with AI-powered, zero-trust precision.
LATEST
- ” If they open up to…Wnba Is Not First Sports Activities League To Have Intercourse Toys Thrown At Games We are all the time including brand new toys and necessities, and our excellent relationships with local and worldwide brands imply that you’ll find intercourse toys and products proper here earlier than they’re launched wherever else. This toy exceeds its expectations in so … Read more
- telegram nudes ✓ Discover Top Adult…telegram nudes Discover adult Telegram channels sharing explicit content. ✓ Join now for exclusive images and videos in a community-driven, private space! ➔
- Casino X стратегии и советы для…Casino X стратегии и советы для новичков в играх Casino X стратегии и советы для начинающих игроков Перед тем как приступить к азартным приключениям, важно определить свой бюджет. Установите лимит, который не повлияет на ваше финансовое положение. Это защитит от ненужных трат и поможет наслаждаться процессом, не переживая о последствиях. Не забывайте, что каждая игра … Read more
- Windows 10 OS Activator ✓ Activate…Windows 10 OS activator ✓ Activate Windows and Office using powerful tools ➤ HWID, Online KMS, TSforge methods ★ reliable activation for 32/64-bit systems.
- Актуальное зеркало Vavada казино для азартных…Актуальное зеркало Vavada казино для азартных игр Актуальное зеркало Vavada казино для азартных игр Если вы ищете надежный способ доступа к увлекательным играм, настоятельно рекомендуется обратить внимание на вавада зеркало. Оно обеспечивает непрерывный доступ к любимым слотам и настольным играм, что позволяет сразу наслаждаться игровым процессом без задержек. В 2026 году особое внимание уделяется разнообразию … Read more
POST
?De que forma conozco que un…
Alli podrias adoptar nuestro casino cual superior se podri�an mover
Read moreTasmania JackJumpers as compared to Perth…
Tasmania JackJumpers as compared to Perth Wildcats Forecast, Playing Info
Read moreLes meilleures Mecanique pour Au-dessous En…
Machine a thunes en tenant bonus Vos machine a sous
Read moreKnow More

What to Know Before Implementation
In today’s cybersecurity landscape, protecting your business from sophisticated cyberattacks is more critical than ever. As cyber threats continue to evolve, traditional antivirus solutions are often inadequate. That’s where EDR (Endpoint Detection and Response) solutions come in. EDR solutions provide advanced protection by detecting, investigating, and responding to threats at the endpoint level. However, selecting

New ‘CitrixBleed 2’ Vulnerability in NetScaler…
WhatsApp US House bans WhatsApp from 12,000+ staff devices over spyware threats & cyberse… The United States House of Representatives has taken a significant step in its cybersecurity measures by imposing a ban on WhatsApp across all government-issued devices. This move, announced on June 23, 2025, is not just a standalone decision but a part

Weekly Update 455
The bot-fighting is a non-stop battle. In this week's video, I discuss how we're tweaking Cloudflare Turnstile and combining more attributes around how bot-like requests are, and… it almost worked. Just as I was preparing to write this intro, I found a small spike of anomalous traffic that, upon further investigation, should have been blocked.

Citrix warns of login issues after…
Citrix warns that patching recently disclosed vulnerabilities that can be exploited to bypass authentication and launch denial-of-service attacks may also break login pages on NetScaler ADC and Gateway appliances. This happens because starting with NetScaler 14.1.47.46 and 13.1.59.19, the Content Security Policy (CSP) header, which mitigates risks associated with cross-site scripting (XSS), code injection, and
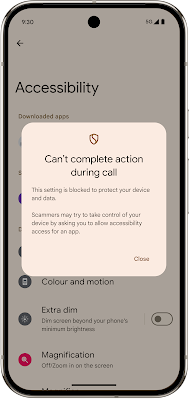
What’s New in Android Security and…
Posted by Dave Kleidermacher, VP Engineering, Android Security and Privacy Android’s intelligent protections keep you safe from everyday dangers. Our dedication to your security is validated by security experts, who consistently rank top Android devices highest in security, and score Android smartphones, led by the Pixel 9 Pro, as leaders in anti-fraud efficacy. Android is
TDF Extends Data-Centric Security Beyond the…
DSPM (Data Security Posture Management) solutions are some of the hottest companies in cybersecurity right now. We’ve written about companies like Cyera, Rubrik, and Varonis, who each create powerful frameworks for protecting data that companies possess internally, surfacing risk and enabling better data governance across enterprise environments.
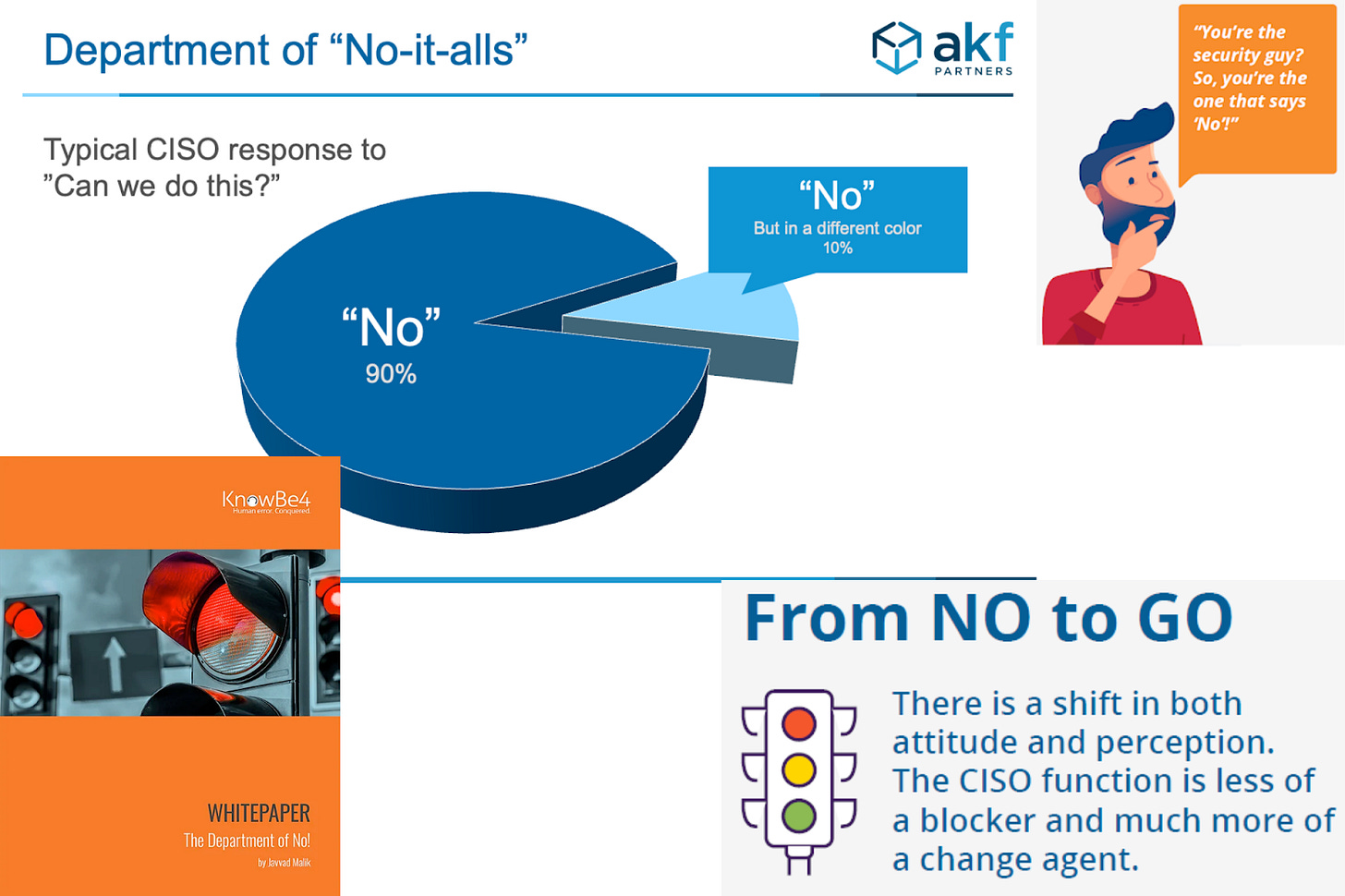
Security is not the department of…
Nearly once a week, I hear someone say that security needs to stop being a department of “No” and that instead, it needs to become a “business enabler”. Every time someone says it, I can’t help but wonder where this idea originated and how it was able to become so widespread. In this piece, I
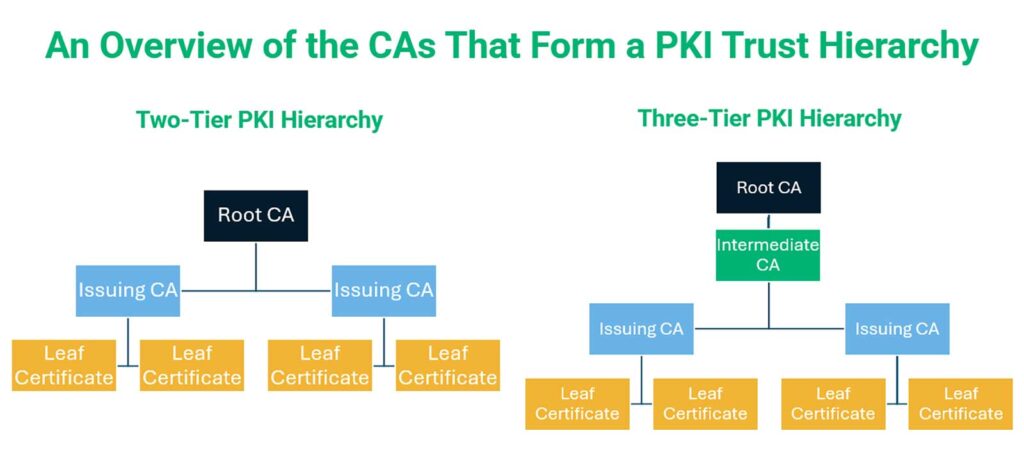
Demystifying PKI Technology: An Essential Guide…
Learn everything you need to know about PKI technology in IT security that enables organizations to establish trust in a digital world where the physical verification of identities is impossible When you open a website, make an online payment, or binge your favorite series on Netflix, PKI technology is the hidden force that makes these

Webinar: Elevate your security with Microsoft…
21 May 2025, 10:00 – 11:00 CET We’re excited to invite you to an exclusive webinar, where we introduce the new Microsoft Defender XDR integration with Logpoint — built for security teams who need faster, smarter, and more scalable threat detection. Discover how easily you can: Deploy quickly with template-driven integration — no heavy
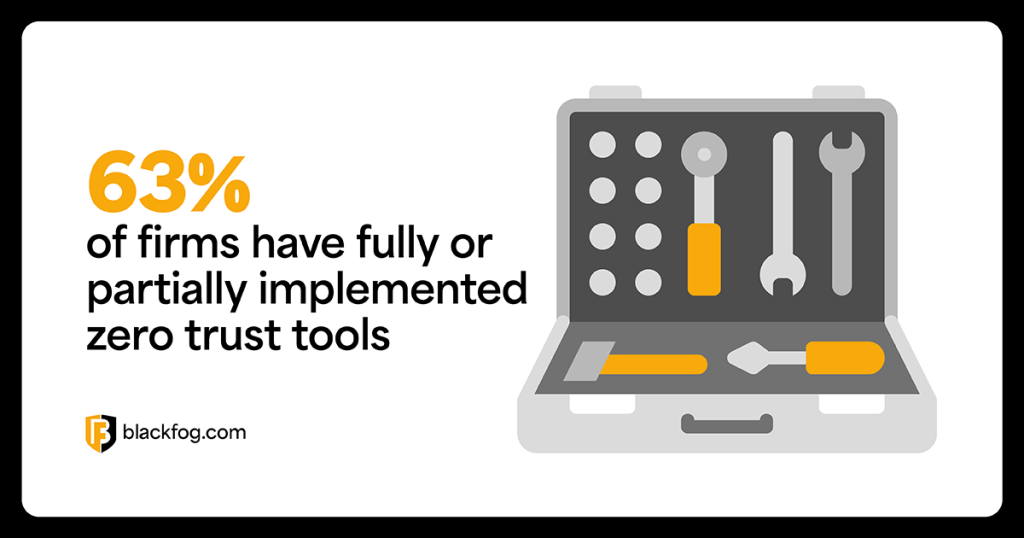
Zero Trust Data Protection: Securing Your…
Zero Trust Data Protection: Securing Your Data in a Perimeterless World The threat landscape for businesses has never been more complex. Hackers are constantly evolving their tactics, making data security a critical priority. In recent years, data exfiltration has become a prime goal of cybercriminals, especially with the rise of double extortion ransomware that not