Welcome To AntiFingerPrints
AntiFingerPrints revolutionizes surface protection with advanced nano-tech coatings that eliminate smudges, enhance durability, and maintain pristine clarity effortlessly.

Categories

Forensic
Forensic science unravels hidden truths by analyzing digital trails, biological evidence, and crime scenes with cutting-edge precision to deliver justice.

Durable
Durable isnât just toughâitâs engineered to outlast, outperform, and defy wear, turning resilience into a silent competitive advantage.

Automotive
Automotive innovation merges cutting-edge tech, electrification, and autonomy to redefine mobilityâwhere performance meets sustainability on the road ahead.

Textured
Textured surfaces blend artistry with functionality, creating tactile depth that enhances grip, aesthetics, and smudge resistance in design.

Network
Network security fortifies digital arteries with firewalls, encryption, and AI-driven threat detection to keep data flowing safely and attacks at bay.

Endpoint
Endpoint security guards the frontline of your digital perimeter, stopping threats before they breach with AI-powered, zero-trust precision.
LATEST
- ” If they open up to…Wnba Is Not First Sports Activities League To Have Intercourse Toys Thrown At Games We are all the time including brand new toys and necessities, and our excellent relationships with local and worldwide brands imply that you’ll find intercourse toys and products proper here earlier than they’re launched wherever else. This toy exceeds its expectations in so … Read more
- telegram nudes ✓ Discover Top Adult…telegram nudes Discover adult Telegram channels sharing explicit content. ✓ Join now for exclusive images and videos in a community-driven, private space! ➔
- Casino X стратегии и советы для…Casino X стратегии и советы для новичков в играх Casino X стратегии и советы для начинающих игроков Перед тем как приступить к азартным приключениям, важно определить свой бюджет. Установите лимит, который не повлияет на ваше финансовое положение. Это защитит от ненужных трат и поможет наслаждаться процессом, не переживая о последствиях. Не забывайте, что каждая игра … Read more
- Windows 10 OS Activator ✓ Activate…Windows 10 OS activator ✓ Activate Windows and Office using powerful tools ➤ HWID, Online KMS, TSforge methods ★ reliable activation for 32/64-bit systems.
- Актуальное зеркало Vavada казино для азартных…Актуальное зеркало Vavada казино для азартных игр Актуальное зеркало Vavada казино для азартных игр Если вы ищете надежный способ доступа к увлекательным играм, настоятельно рекомендуется обратить внимание на вавада зеркало. Оно обеспечивает непрерывный доступ к любимым слотам и настольным играм, что позволяет сразу наслаждаться игровым процессом без задержек. В 2026 году особое внимание уделяется разнообразию … Read more
POST
?De que forma conozco que un…
Alli podrias adoptar nuestro casino cual superior se podri�an mover
Read moreTasmania JackJumpers as compared to Perth…
Tasmania JackJumpers as compared to Perth Wildcats Forecast, Playing Info
Read moreLes meilleures Mecanique pour Au-dessous En…
Machine a thunes en tenant bonus Vos machine a sous
Read moreKnow More

Bridging the Nursing Workforce Skills Gap…
The US is facing a critical nursing workforce challenge, with increasing shortages and evolving skill demands. As healthcare facilities scramble to fill gaps, technology-driven solutions are proving essential in streamlining recruitment and ensuring nurses have the right qualifications. One such innovation is the use of online skills checklists, which allow recruiters to assess candidates efficiently,
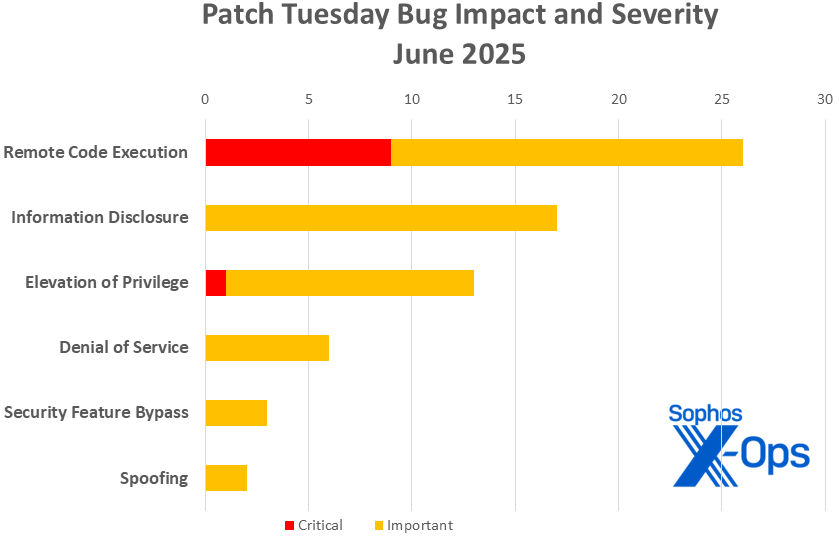
June Patch Tuesday digs into 67…
.Microsoft on Tuesday released 67 patches affecting 12 product families. Ten of the addressed issues, five involving 365 and Office and one involving SharePoint, are considered by Microsoft to be of Critical severity, and 17 have a CVSS base score of 8.0 or higher. One, an Important-severity RCE in Windows related to WEBDAV (CVE-2025-33053), is
Is hacktivism acceptable? — Matt Palmer
This week I attended CSO Online’s CSO Security Summit in London, which was tracked into protection and culture tracks. One of the most interesting aspects of this was the focus on mental heath. As any incident responder (professional or accidental!) will know, these can be very stressful. We ignore these issues at our peril. However

Cybersecurity Advisory: Hackers Exploit Zoom’s Remote…
A newly uncovered cyberattack campaign is exploiting Zoom’s Remote Control feature to infiltrate the systems of cryptocurrency traders and venture capitalists. Named “Elusive Comet,” this campaign employs sophisticated social engineering tactics to trick users into granting remote access during Zoom meetings, leading to the deployment of infostealer malware and unauthorized access to sensitive data. How
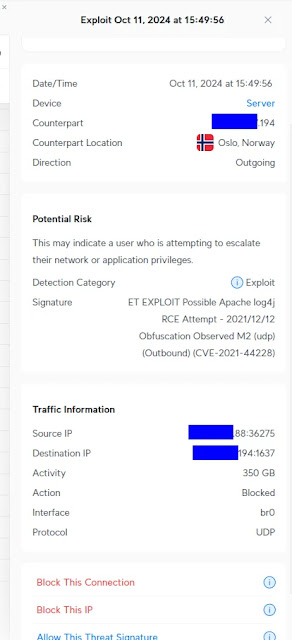
What Are Normal Users Supposed to…
Probably once a week, I see posts like this in the r/Ubiquiti subreddit. Ubiquiti makes network gear that includes an “IDS/IPS” feature. I own some older Ubiquiti gear so I am familiar with the product. When you enable this feature, you get alerts like this one, posted by a Redditor: This is everything you get

Can Your Exposure Management Strategy Handle…
The cybersecurity landscape has always been a relentless arms race. But the advent of AI (artificial intelligence) is changing its face even more dramatically. Virtually any threat actor can now automate, scale, and refine with AI what was once the exclusive domain of highly skilled, time-intensive manual operations. This capability metamorphosis requires a critical re-evaluation
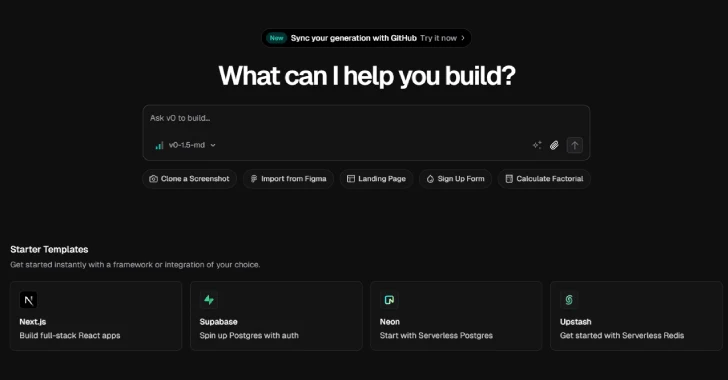
Vercel’s v0 AI Tool Weaponized by…
Jul 02, 2025Ravie LakshmananAI Security / Phishing Unknown threat actors have been observed weaponizing v0, a generative artificial intelligence (AI) tool from Vercel, to design fake sign-in pages that impersonate their legitimate counterparts. “This observation signals a new evolution in the weaponization of Generative AI by threat actors who have demonstrated an ability to generate
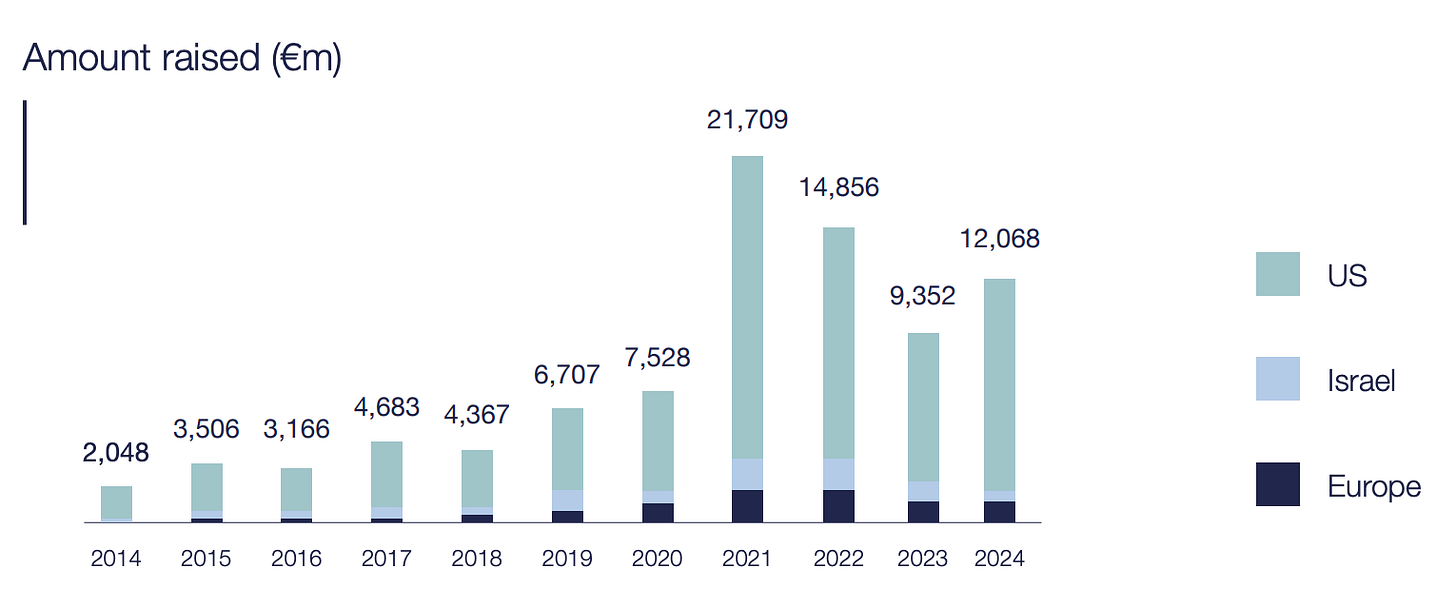
Fewer Cheques, Tougher Checks: Cyber VC…
Hello Cyber Builders 🖖 Cybersecurity is at the top of everyone’s mind, and AI brings more opportunities and threats at the same time. Therefore, we would expect funding levels to be high and investors to be eager to seize opportunities… That would be great, wouldn’t it? While investment levels are still solid, the number of
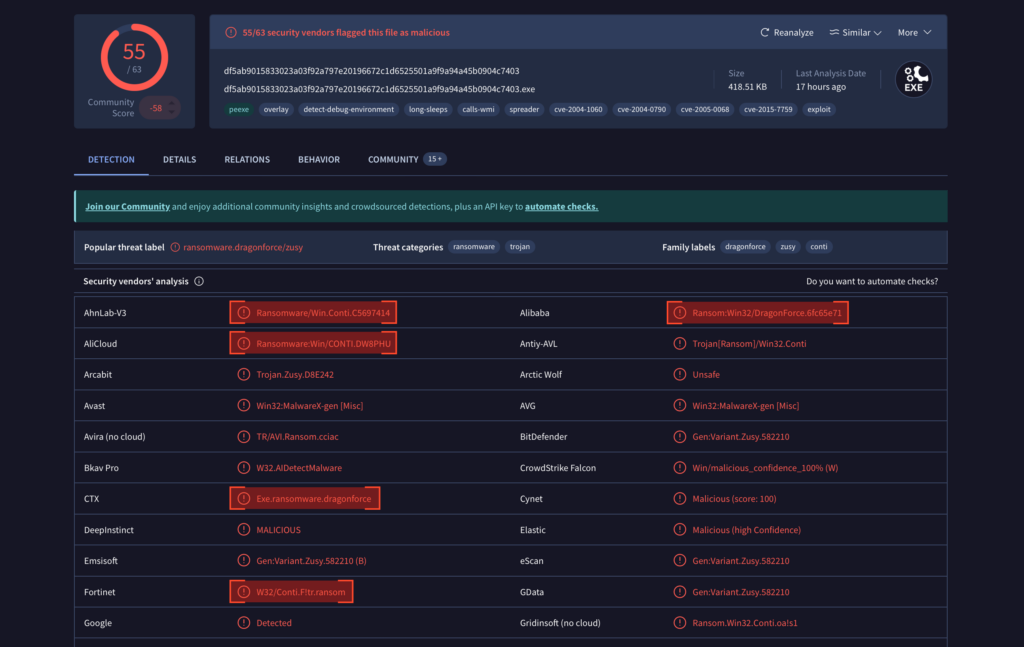
DEVMAN Ransomware: Analysis of New DragonForce…
HomeMalware Analysis DEVMAN Ransomware: Analysis of New DragonForce Variant Editor’s note: The current article is authored by Mauro Eldritch, offensive security expert and threat intelligence analyst. You can find Mauro on X. New ransomware strains continue to surface frequently, and many of them are loosely built on or repackaged from existing families. One such case
Operation Endgame, deepfakes, and dead slugs…
In this episode, Graham unravels Operation Endgame – the surprisingly stylish police crackdown that is seizing botnets, mocking malware authors with anime videos, and taunting cybercriminals via Telegram. Meanwhile, Carole exposes the AI-generated remote hiring threat. Could your next coworker be a North Korean hacker with a perfect LinkedIn? And BBC cyber correspondent Joe Tidy