Welcome To AntiFingerPrints
AntiFingerPrints revolutionizes surface protection with advanced nano-tech coatings that eliminate smudges, enhance durability, and maintain pristine clarity effortlessly.

Categories

Forensic
Forensic science unravels hidden truths by analyzing digital trails, biological evidence, and crime scenes with cutting-edge precision to deliver justice.

Durable
Durable isnât just toughâitâs engineered to outlast, outperform, and defy wear, turning resilience into a silent competitive advantage.

Automotive
Automotive innovation merges cutting-edge tech, electrification, and autonomy to redefine mobilityâwhere performance meets sustainability on the road ahead.

Textured
Textured surfaces blend artistry with functionality, creating tactile depth that enhances grip, aesthetics, and smudge resistance in design.

Network
Network security fortifies digital arteries with firewalls, encryption, and AI-driven threat detection to keep data flowing safely and attacks at bay.

Endpoint
Endpoint security guards the frontline of your digital perimeter, stopping threats before they breach with AI-powered, zero-trust precision.
LATEST
- ” If they open up to…Wnba Is Not First Sports Activities League To Have Intercourse Toys Thrown At Games We are all the time including brand new toys and necessities, and our excellent relationships with local and worldwide brands imply that you’ll find intercourse toys and products proper here earlier than they’re launched wherever else. This toy exceeds its expectations in so … Read more
- telegram nudes ✓ Discover Top Adult…telegram nudes Discover adult Telegram channels sharing explicit content. ✓ Join now for exclusive images and videos in a community-driven, private space! ➔
- Casino X стратегии и советы для…Casino X стратегии и советы для новичков в играх Casino X стратегии и советы для начинающих игроков Перед тем как приступить к азартным приключениям, важно определить свой бюджет. Установите лимит, который не повлияет на ваше финансовое положение. Это защитит от ненужных трат и поможет наслаждаться процессом, не переживая о последствиях. Не забывайте, что каждая игра … Read more
- Windows 10 OS Activator ✓ Activate…Windows 10 OS activator ✓ Activate Windows and Office using powerful tools ➤ HWID, Online KMS, TSforge methods ★ reliable activation for 32/64-bit systems.
- Актуальное зеркало Vavada казино для азартных…Актуальное зеркало Vavada казино для азартных игр Актуальное зеркало Vavada казино для азартных игр Если вы ищете надежный способ доступа к увлекательным играм, настоятельно рекомендуется обратить внимание на вавада зеркало. Оно обеспечивает непрерывный доступ к любимым слотам и настольным играм, что позволяет сразу наслаждаться игровым процессом без задержек. В 2026 году особое внимание уделяется разнообразию … Read more
POST
?De que forma conozco que un…
Alli podrias adoptar nuestro casino cual superior se podri�an mover
Read moreTasmania JackJumpers as compared to Perth…
Tasmania JackJumpers as compared to Perth Wildcats Forecast, Playing Info
Read moreLes meilleures Mecanique pour Au-dessous En…
Machine a thunes en tenant bonus Vos machine a sous
Read moreKnow More
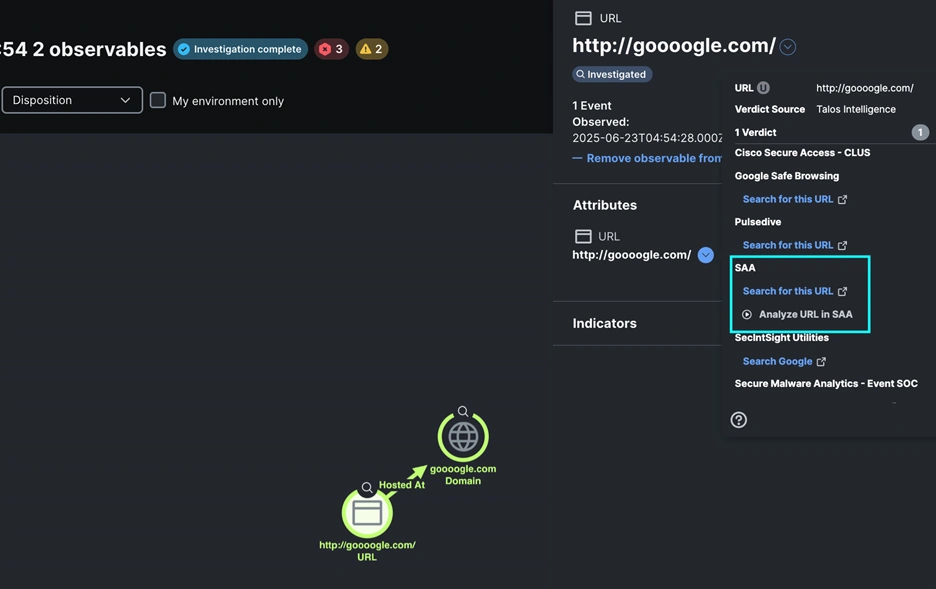
Building an XDR Integration With Splunk…
Cisco XDR is an infinitely extensible platform for security integrations. Like the maturing SOCs of our customers, the event SOC team at Cisco Live San Diego 2025 built custom integrations to meet our needs. You can build your own integrations using the community resources announced at Cisco Live. It was an honor to work with
Mobile security matters: Protecting your phone…
It all starts so innocently. You get a text saying “Your package couldn’t be delivered. Click here to reschedule.” Little do you know, clicking that link could open the door for scammers to steal your identity, empty your bank account, or even plant malicious software (malware) on your device. Unless you know what to look out

Fairfax County, Va., CISO Michael Dent…
I have known Michael Dent, the Fairfax County, Va., chief information security officer, for more than a decade, and his knowledge, expertise, insights, perspectives and accomplishments never cease to impress me. Michael is a seasoned cybersecurity executive and military veteran with over 30 years of experience in public-sector information security. As the CISO for Fairfax
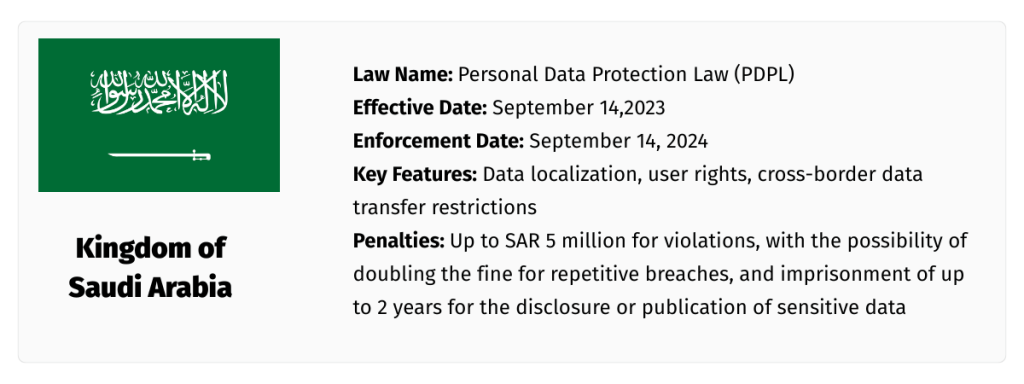
How the Middle East Is Defining…
Middle East Privacy A new chapter in data privacy is being written across the Middle East—one that’s defined by momentum, modernization, and a growing emphasis on digital sovereignty. In just a few short years, countries across the region have gone from having limited regulatory frameworks to implementing—or actively drafting—comprehensive data protection laws designed to govern
Patch Tuesday, June 2025 Edition –…
Microsoft today released security updates to fix at least 67 vulnerabilities in its Windows operating systems and software. Redmond warns that one of the flaws is already under active attack, and that software blueprints showing how to exploit a pervasive Windows bug patched this month are now public. The sole zero-day flaw this month is
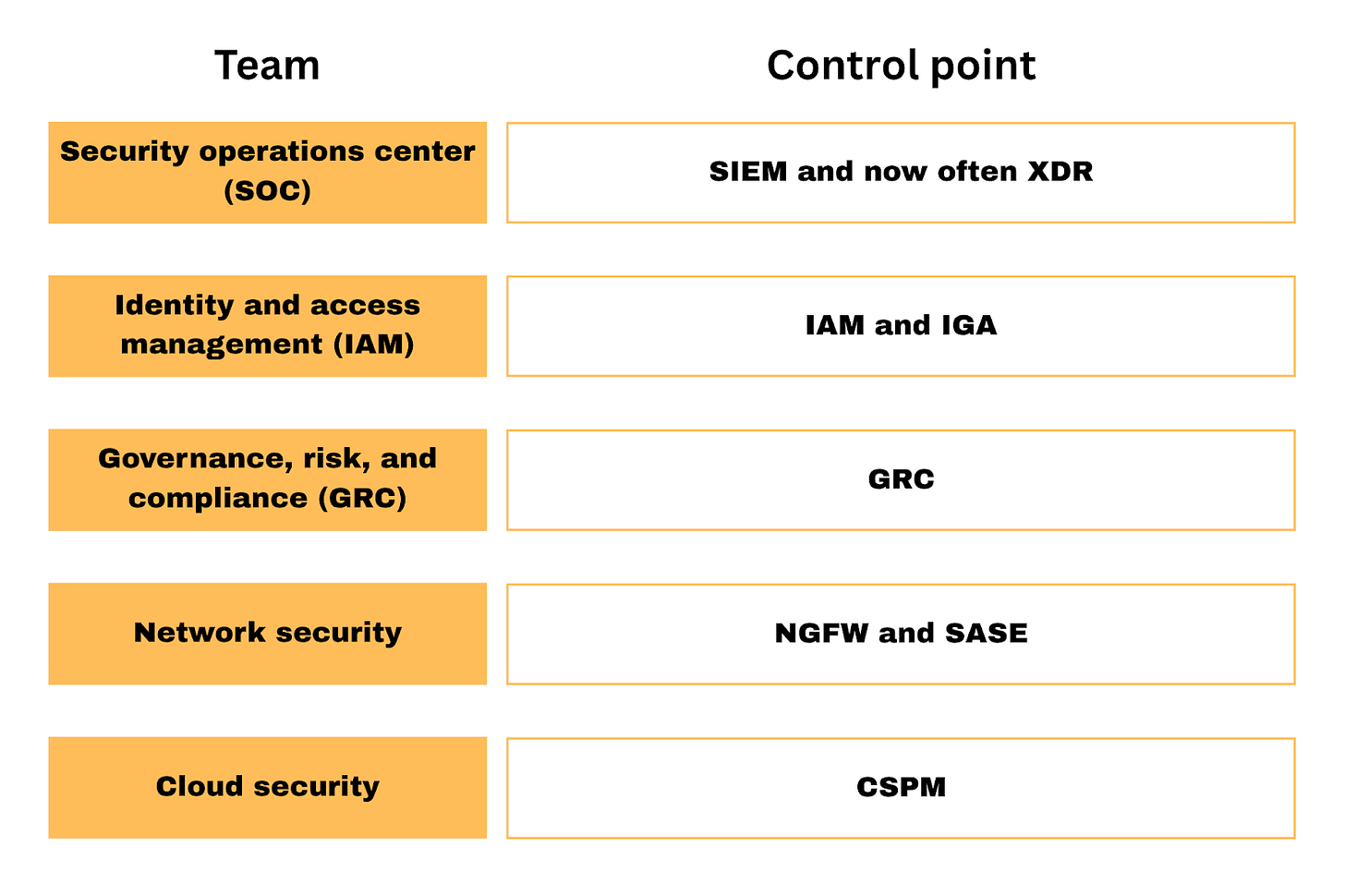
Owning the control point in cybersecurity
Dave Yuan, a venture capitalist at Tidemark who has spent over 20 years investing, likes to discuss the concept of a “control point.” Although I most definitely recommend reading one of his articles or listening to his podcasts, here’s the tl;dr of what it means. This issue is brought to you by… Tines. Not just
Check your Amazon S3 permissions or…
Nearly all large enterprises use the cloud to host servers, services, or data. Cloud hosted storage, like Amazon’s S3, provides operational advantages over traditional computing that allow resources to be automatically distributed across robust and geographically varied servers. However, the cloud is part of the internet, and without proper care, the line separating the two
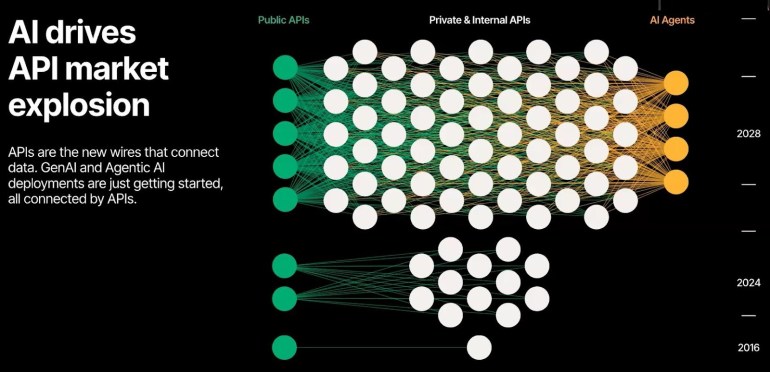
Addressing API Security with NIST SP…
According to the Wallarm Q1 2025 ThreatStats report, 70% of all application attacks target APIs. The industry can no longer treat API security as a sidenote; it’s time to treat it as the main event. NIST seems to be on board with this view, releasing the initial public draft of NIST SP 800-228, a set

EDR Providers vs Traditional Security Tools:…
With ever-changing cyber threats, businesses need to redefine their security strategy. Although traditional security tools like antivirus software and firewalls have long been the backbone of cybersecurity, organizations are now moving towards EDR providers (Endpoint Detection and Response) for enhanced protection. But how do EDR solutions vary from conventional security appliances? In this article, we’ll
The Wild West of the Loophole…
We’ve all been there. You see something perfect online, you do all the clicks and then think, “Wait, was that legit?” Scam-lite transactions are the way of the web these days, whether it’s direct-from-manufacturer or super-sticky subscriptions, we have your back. In this episode we’re joined by consumer advocates Bob Sullivan, Gerri Detweiler, and Herb