Welcome To AntiFingerPrints
AntiFingerPrints revolutionizes surface protection with advanced nano-tech coatings that eliminate smudges, enhance durability, and maintain pristine clarity effortlessly.

Categories

Forensic
Forensic science unravels hidden truths by analyzing digital trails, biological evidence, and crime scenes with cutting-edge precision to deliver justice.

Durable
Durable isnât just toughâitâs engineered to outlast, outperform, and defy wear, turning resilience into a silent competitive advantage.

Automotive
Automotive innovation merges cutting-edge tech, electrification, and autonomy to redefine mobilityâwhere performance meets sustainability on the road ahead.

Textured
Textured surfaces blend artistry with functionality, creating tactile depth that enhances grip, aesthetics, and smudge resistance in design.

Network
Network security fortifies digital arteries with firewalls, encryption, and AI-driven threat detection to keep data flowing safely and attacks at bay.

Endpoint
Endpoint security guards the frontline of your digital perimeter, stopping threats before they breach with AI-powered, zero-trust precision.
LATEST
- ” If they open up to…Wnba Is Not First Sports Activities League To Have Intercourse Toys Thrown At Games We are all the time including brand new toys and necessities, and our excellent relationships with local and worldwide brands imply that you’ll find intercourse toys and products proper here earlier than they’re launched wherever else. This toy exceeds its expectations in so … Read more
- telegram nudes ✓ Discover Top Adult…telegram nudes Discover adult Telegram channels sharing explicit content. ✓ Join now for exclusive images and videos in a community-driven, private space! ➔
- Casino X стратегии и советы для…Casino X стратегии и советы для новичков в играх Casino X стратегии и советы для начинающих игроков Перед тем как приступить к азартным приключениям, важно определить свой бюджет. Установите лимит, который не повлияет на ваше финансовое положение. Это защитит от ненужных трат и поможет наслаждаться процессом, не переживая о последствиях. Не забывайте, что каждая игра … Read more
- Windows 10 OS Activator ✓ Activate…Windows 10 OS activator ✓ Activate Windows and Office using powerful tools ➤ HWID, Online KMS, TSforge methods ★ reliable activation for 32/64-bit systems.
- Актуальное зеркало Vavada казино для азартных…Актуальное зеркало Vavada казино для азартных игр Актуальное зеркало Vavada казино для азартных игр Если вы ищете надежный способ доступа к увлекательным играм, настоятельно рекомендуется обратить внимание на вавада зеркало. Оно обеспечивает непрерывный доступ к любимым слотам и настольным играм, что позволяет сразу наслаждаться игровым процессом без задержек. В 2026 году особое внимание уделяется разнообразию … Read more
POST
?De que forma conozco que un…
Alli podrias adoptar nuestro casino cual superior se podri�an mover
Read moreTasmania JackJumpers as compared to Perth…
Tasmania JackJumpers as compared to Perth Wildcats Forecast, Playing Info
Read moreLes meilleures Mecanique pour Au-dessous En…
Machine a thunes en tenant bonus Vos machine a sous
Read moreKnow More
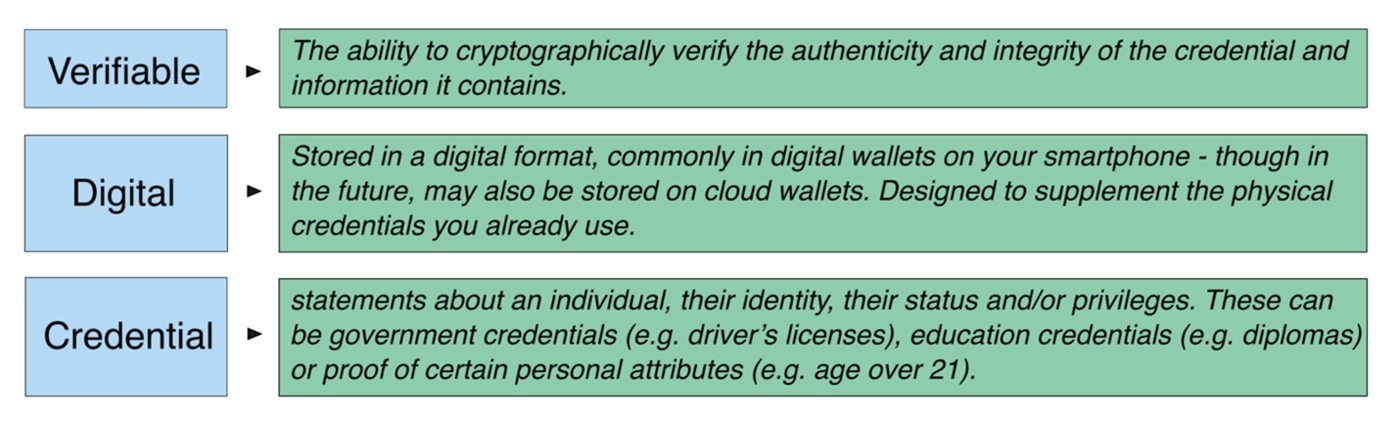
Digital Identities: Getting to Know the…
If you are interested in the world of digital identities, you have probably heard some of the buzzwords that have been floating around for a few years now… “verifiable credential,” “digital wallet,” “mobile driver’s license” or “mDL.” These terms, among others, all reference a growing ecosystem around what we are calling “verifiable digital credentials.” But

Meet This Year’s North America Community…
This episode of Coffee with the Council is brought to you by our podcast sponsor, Feroot. Welcome to our podcast series, Coffee with the Council. I’m Alicia Malone, Director of Communications and Public Relations for the PCI Security Standards Council. Today, I am so excited to bring you a sneak peek interview with PCI
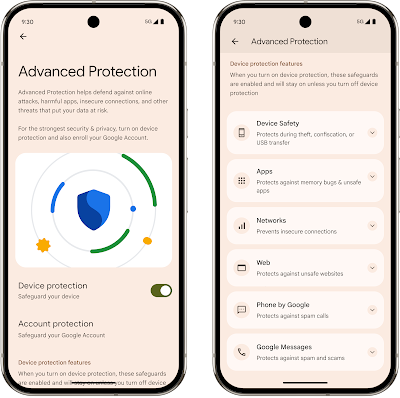
Google’s Strongest Security for Mobile Devices
Posted by Il-Sung Lee, Group Product Manager, Android Security Protecting users who need heightened security has been a long-standing commitment at Google, which is why we have our Advanced Protection Program that provides Google’s strongest protections against targeted attacks. To enhance these existing device defenses, Android 16 extends Advanced Protection with a device-level security setting
Key Components of an Incident Response…
Key Components of an Incident Response Plan A robust incident response plan is imperative for organizations seeking to mitigate the impact of contemporary cyber threats. This document must be dynamic, subject to regular review and adaptation to address emerging vulnerabilities and attack vectors. The following outlines essential components for a comprehensive plan: 1. Preparation Preparation

6 Dimensions to Cut Through the…
Hello CyberBuilders 🖖 Let’s talk AI security (don’t stop reading here, give me 2 mins!) It’s the new obsession in the cybersecurity startup world. In the past two years, funding has poured into companies claiming to protect, secure, or safeguard AI. Articles go into every flashy point exploit, then pitch simplistic one-size-fits-all fixes. But while
Layered Security – How a Defense-in-Depth…
Layered Security – How a Defense-in-Depth Approach Guards Against Unknown Threats Today’s rapidly-evolving cybersecurity landscape means businesses are under more pressure than ever. A sophisticated range of threats now aim to bypass traditional defenses, which leaves organizations vulnerable if they’re still relying on legacy tools like antimalware software. These often aren’t able to spot advanced

Cloudflare Launches Open E2E Video Chat…
WhatsApp US House bans WhatsApp from 12,000+ staff devices over spyware threats & cyberse… The United States House of Representatives has taken a significant step in its cybersecurity measures by imposing a ban on WhatsApp across all government-issued devices. This move, announced on June 23, 2025, is not just a standalone decision but a part
Best MSSP Providers You Can Trust
Managed security services providers, or MSSP providers for short, have become essential allies to businesses in the face of soaring cyber attacks. These third-party experts step in to fill the critical cybersecurity gaps, delivering managed security services—all backed by deep expertise that many in-house teams simply can’t afford. To help you find the right security

Forminator plugin flaw exposes WordPress sites…
The Forminator plugin for WordPress is vulnerable to an unauthenticated arbitrary file deletion flaw that could enable full site takeover attacks. The security issue is tracked as CVE-2025-6463 and has a high-severity impact (CVSS 8.8 score). It impacts all versions of Forminator up to 1.44.2. Forminator Forms is a plugin developed by WPMU DEV. It offers a
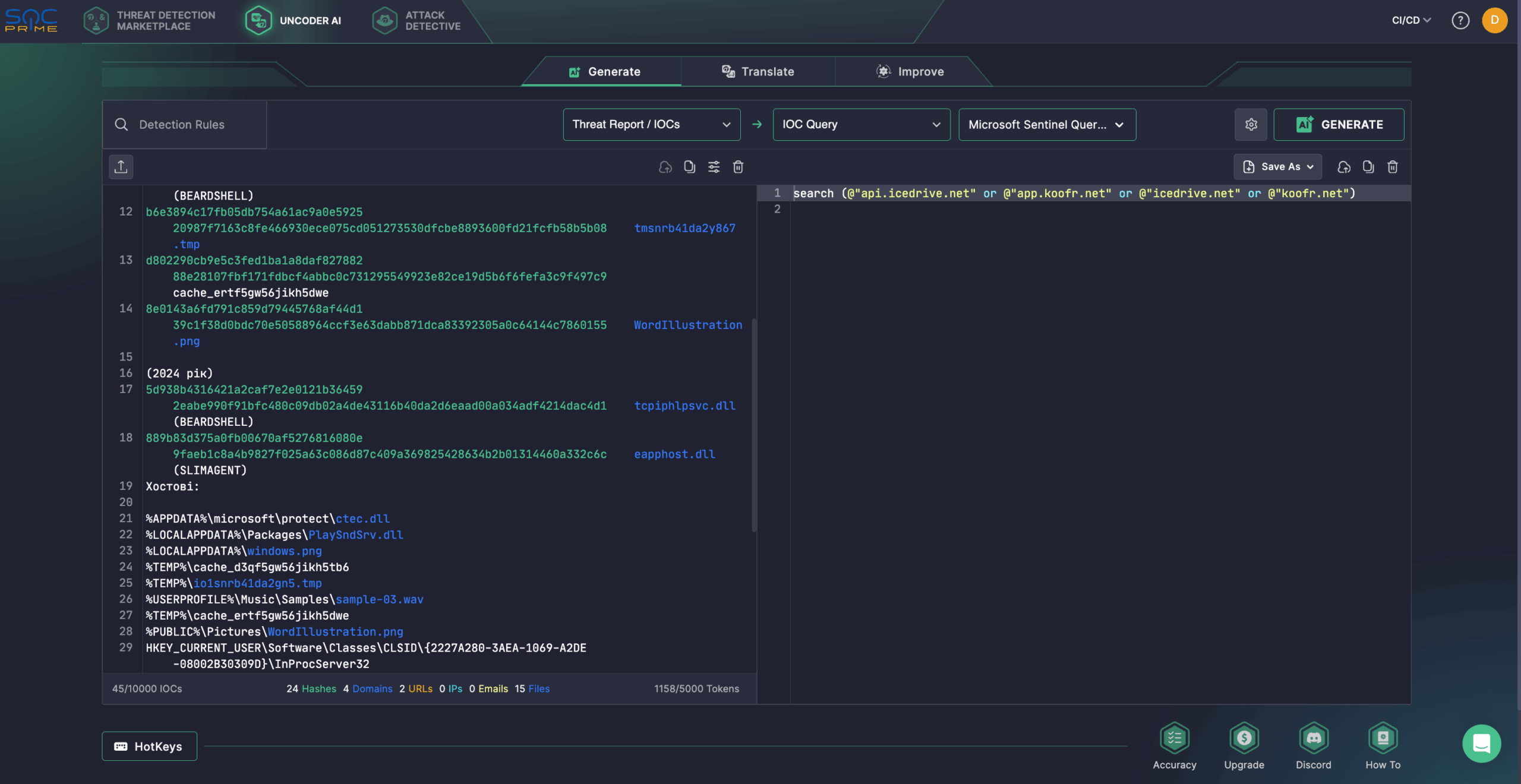
UAC-0001 (APT28) Activity Detection: The russian…
The nefarious nation-backed russian hacking collective known as UAC-0001 (aka APT28) reemerges in the cybersecurity spotlight. Over a year ago, in the spring of 2024, the CERT-UA team was investigating an incident targeting state executive bodies and identified a Windows-based server. In May 2025, ESET shared timely intelligence indicating unauthorized access to an email account