Welcome To AntiFingerPrints
AntiFingerPrints revolutionizes surface protection with advanced nano-tech coatings that eliminate smudges, enhance durability, and maintain pristine clarity effortlessly.

Categories

Forensic
Forensic science unravels hidden truths by analyzing digital trails, biological evidence, and crime scenes with cutting-edge precision to deliver justice.

Durable
Durable isnât just toughâitâs engineered to outlast, outperform, and defy wear, turning resilience into a silent competitive advantage.

Automotive
Automotive innovation merges cutting-edge tech, electrification, and autonomy to redefine mobilityâwhere performance meets sustainability on the road ahead.

Textured
Textured surfaces blend artistry with functionality, creating tactile depth that enhances grip, aesthetics, and smudge resistance in design.

Network
Network security fortifies digital arteries with firewalls, encryption, and AI-driven threat detection to keep data flowing safely and attacks at bay.

Endpoint
Endpoint security guards the frontline of your digital perimeter, stopping threats before they breach with AI-powered, zero-trust precision.
LATEST
- ” If they open up to…Wnba Is Not First Sports Activities League To Have Intercourse Toys Thrown At Games We are all the time including brand new toys and necessities, and our excellent relationships with local and worldwide brands imply that you’ll find intercourse toys and products proper here earlier than they’re launched wherever else. This toy exceeds its expectations in so … Read more
- telegram nudes ✓ Discover Top Adult…telegram nudes Discover adult Telegram channels sharing explicit content. ✓ Join now for exclusive images and videos in a community-driven, private space! ➔
- Casino X стратегии и советы для…Casino X стратегии и советы для новичков в играх Casino X стратегии и советы для начинающих игроков Перед тем как приступить к азартным приключениям, важно определить свой бюджет. Установите лимит, который не повлияет на ваше финансовое положение. Это защитит от ненужных трат и поможет наслаждаться процессом, не переживая о последствиях. Не забывайте, что каждая игра … Read more
- Windows 10 OS Activator ✓ Activate…Windows 10 OS activator ✓ Activate Windows and Office using powerful tools ➤ HWID, Online KMS, TSforge methods ★ reliable activation for 32/64-bit systems.
- Актуальное зеркало Vavada казино для азартных…Актуальное зеркало Vavada казино для азартных игр Актуальное зеркало Vavada казино для азартных игр Если вы ищете надежный способ доступа к увлекательным играм, настоятельно рекомендуется обратить внимание на вавада зеркало. Оно обеспечивает непрерывный доступ к любимым слотам и настольным играм, что позволяет сразу наслаждаться игровым процессом без задержек. В 2026 году особое внимание уделяется разнообразию … Read more
POST
?De que forma conozco que un…
Alli podrias adoptar nuestro casino cual superior se podri�an mover
Read moreTasmania JackJumpers as compared to Perth…
Tasmania JackJumpers as compared to Perth Wildcats Forecast, Playing Info
Read moreLes meilleures Mecanique pour Au-dessous En…
Machine a thunes en tenant bonus Vos machine a sous
Read moreKnow More

Introducing Guernsey Cyber Security Centre —…
Since 2021, I’ve been building Jersey Cyber Security Centre (JCSC). As a cyber defence capability for an island state and leading International Finance Centre, we’re a small team with a big task. We’re also just one of hundreds: teams in countries from all around the world, all united by a mission to defend people and

A Guide to Developing Security-First Culture…
HomeCybersecurity Lifehacks A Guide to Developing Security-First Culture Powered by Threat Intelligence Security-First Culture (SFC) is an organization-wide commitment where security considerations influence decision-making at every level, from strategic planning to daily operational tasks. It’s not just about having fancy tech or a dedicated IT team; it’s about making security a core part of how

Is Your Network Configured to Prevent…
Many enterprises allocate significant resources to prevent damaging DDoS attacks – only to discover that critical gaps still exist. MazeBolt’s latest eBook explores some of the different aspects of network configuration that can leave organizations highly exposed to damaging downtime – even if they have premium DDoS protections deployed. One example of a network configuration

Reinventing Cyber Defence with Proper Licensing
Date: 1 July 2025 Once business goals are set and the appropriate SAP product suite is selected, the next step is to consider the licensing type. In today’s computerised environment, safeguarding a dynamic SAP environment is no longer about blocking external threats but also guaranteeing internal controls, especially in the case of licensing models. SAP

BreachForums broken up? French police arrest…
Suspected high-ranking members of one of the world’s largest online marketplaces for leaked data have been arrested by French police. According to local media reports, French cybercrime cops detained four prominent members of the BreachForums site. The suspects – who are said to go by the online handles of Depressed, Hollow, Noct, and Shiny Hunters

Addressing Our ‘Age of Insecurity’ —…
In her award-winning book The Age of Insecurity: Coming Together as Things Fall Apart, Astra Taylor makes the argument that everyone feels insecure. The book’s description discusses our cultural challenges this way: “We are financially stressed and emotionally overwhelmed. The status quo isn’t working for anyone, even those who appear to have it all. What
The Impact of Security Breaches on…
This blog was originally published by Bravura here. Educational institutions oversee hundreds or thousands of students and faculty members daily. Therefore, it’s no surprise they deal with large volumes of valuable data, like: Student and educator login information. Home addresses. Birthdays. Full names. Social security numbers. Credit card information and other financial records. Education

Minimize Cybersecurity Threats by Making Smart…
Hosting is critical in defending websites from modern cyber threats, yet it’s often overlooked in basic security strategies. Different types of hosting offer varying levels of protection, with dedicated and VPS hosting typically offering stronger isolation. Evaluating provider transparency, support quality, and built-in security tools is key to making a smart, long-term hosting decision. Avoid
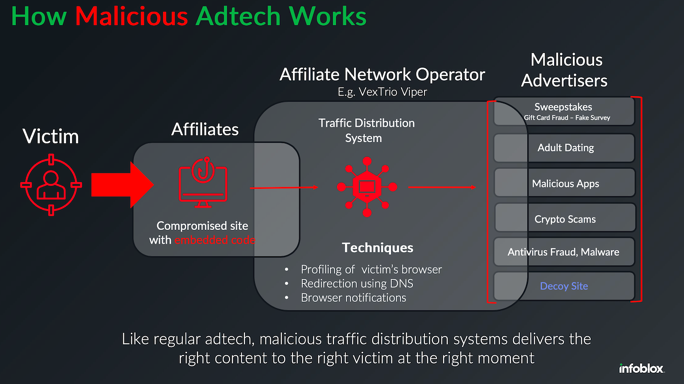
Inside a Dark Adtech Empire Fed…
Late last year, security researchers made a startling discovery: Kremlin-backed disinformation campaigns were bypassing moderation on social media platforms by leveraging the same malicious advertising technology that powers a sprawling ecosystem of online hucksters and website hackers. A new report on the fallout from that investigation finds this dark ad tech industry is far more

My Story from the Spanish Blackout
Hello Cyber-Builders 🖖 In 2017, I published a paper with NATO experts on what had happened to the Ukrainian power infrastructure during early cyberattacks (see doc at the end). At that time, only a few cybersecurity companies were truly exploring the risks tied to power grids and generation plants. But this April, while visiting Spain,