Welcome To AntiFingerPrints
AntiFingerPrints revolutionizes surface protection with advanced nano-tech coatings that eliminate smudges, enhance durability, and maintain pristine clarity effortlessly.

Categories

Forensic
Forensic science unravels hidden truths by analyzing digital trails, biological evidence, and crime scenes with cutting-edge precision to deliver justice.

Durable
Durable isnât just toughâitâs engineered to outlast, outperform, and defy wear, turning resilience into a silent competitive advantage.

Automotive
Automotive innovation merges cutting-edge tech, electrification, and autonomy to redefine mobilityâwhere performance meets sustainability on the road ahead.

Textured
Textured surfaces blend artistry with functionality, creating tactile depth that enhances grip, aesthetics, and smudge resistance in design.

Network
Network security fortifies digital arteries with firewalls, encryption, and AI-driven threat detection to keep data flowing safely and attacks at bay.

Endpoint
Endpoint security guards the frontline of your digital perimeter, stopping threats before they breach with AI-powered, zero-trust precision.
LATEST
- ” If they open up to…Wnba Is Not First Sports Activities League To Have Intercourse Toys Thrown At Games We are all the time including brand new toys and necessities, and our excellent relationships with local and worldwide brands imply that you’ll find intercourse toys and products proper here earlier than they’re launched wherever else. This toy exceeds its expectations in so … Read more
- telegram nudes ✓ Discover Top Adult…telegram nudes Discover adult Telegram channels sharing explicit content. ✓ Join now for exclusive images and videos in a community-driven, private space! ➔
- Casino X стратегии и советы для…Casino X стратегии и советы для новичков в играх Casino X стратегии и советы для начинающих игроков Перед тем как приступить к азартным приключениям, важно определить свой бюджет. Установите лимит, который не повлияет на ваше финансовое положение. Это защитит от ненужных трат и поможет наслаждаться процессом, не переживая о последствиях. Не забывайте, что каждая игра … Read more
- Windows 10 OS Activator ✓ Activate…Windows 10 OS activator ✓ Activate Windows and Office using powerful tools ➤ HWID, Online KMS, TSforge methods ★ reliable activation for 32/64-bit systems.
- Актуальное зеркало Vavada казино для азартных…Актуальное зеркало Vavada казино для азартных игр Актуальное зеркало Vavada казино для азартных игр Если вы ищете надежный способ доступа к увлекательным играм, настоятельно рекомендуется обратить внимание на вавада зеркало. Оно обеспечивает непрерывный доступ к любимым слотам и настольным играм, что позволяет сразу наслаждаться игровым процессом без задержек. В 2026 году особое внимание уделяется разнообразию … Read more
POST
?De que forma conozco que un…
Alli podrias adoptar nuestro casino cual superior se podri�an mover
Read moreTasmania JackJumpers as compared to Perth…
Tasmania JackJumpers as compared to Perth Wildcats Forecast, Playing Info
Read moreLes meilleures Mecanique pour Au-dessous En…
Machine a thunes en tenant bonus Vos machine a sous
Read moreKnow More
Using AI to Battle Phishing Campaigns…
The Cisco Live Network Operations Center (NOC) deployed Cisco Umbrella for Domain Name Service (DNS) queries and security. The Security Operations Center (SOC) team integrated the DNS logs into Splunk Enterprise Security and Cisco XDR. To protect the Cisco Live attendees on the network, the default Security profile was enabled, to block queries to known
Five Uncomfortable Truths About LLMs in…
Many tech professionals see integrating large language models (LLMs) as a simple process -just connect an API and let it run. At Wallarm, our experience has proved otherwise. Through rigorous testing and iteration, our engineering team uncovered several critical insights about deploying LLMs securely and effectively. This blog shares our journey of integrating cutting-edge AI
Integrating SIEM Threat Intelligence for Better…
In today’s cybersecurity environment, businesses face increasingly sophisticated threats that evolve quickly and often bypass traditional defenses. As such, having an effective security strategy in place is no longer just an option—it’s a necessity. One of the most powerful tools for achieving better threat detection is combining Security Information and Event Management (SIEM) with threat

PDPA Compliance Checklist for Singapore Businesses…
A Practical Blueprint for PDPA Compliance The Personal Data Protection Act (PDPA) is not just a legal formality — it’s a core requirement for doing business in Singapore. Whether you’re a startup, a SME, or a large organization, your customers expect you to take their data seriously. However, figuring out how to comply with PDPA

Second espionage-linked cyberattack hits ICC, exposing…
The latest incident underscores the mounting cyber threats facing international justice institutions, particularly as the ICC pursues high-profile cases against major world powers and finds itself increasingly isolated on the international stage due to recent US sanctions. Geopolitical tensions heighten ICC vulnerability The ICC attack reflects a broader global trend of cybercriminals and nation-state actors

G2 Spring 2025 Report Awards UnderDefense…
We’re proud to share exciting news! UnderDefense has been recognized as a trustworthy, first-rate cybersecurity service provider with 12 new badges from G2. They reflect what matters most to us — our clients’ trust, satisfaction, and robust protection. Every badge is grounded in the positive feedback from our customers and their confidence in our team.
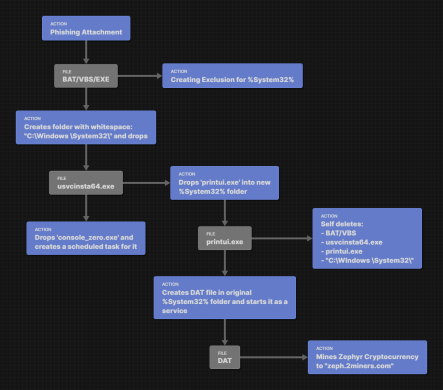
Hijacking Your Resources for Profit
Crypto Mining Crypto mining is the process by which individuals or organizations use computer power to solve complex mathematical problems, validating transactions on a blockchain network and earning cryptocurrency coins. This activity has gained popularity with the increasing value of digital currencies, leading some malicious actors to exploit users’ devices for their own gain. Cybercriminals

Predicted CVEs Likely to be Exploited…
Stay Ahead of Tomorrow’s Threats, Today Welcome to your daily forecast of potential cyber threats. As part of our continuous effort to equip defenders with foresight, we present a list of Common Vulnerability Enumerations (CVEs) that our threat prediction models indicate are likely to be exploited in the near future. Top Predicted CVEs for July

Tracking the Cost of Quantum Factoring
Google Quantum AI’s mission is to build best in class quantum computing for otherwise unsolvable problems. For decades the quantum and security communities have also known that large-scale quantum computers will at some point in the future likely be able to break many of today’s secure public key cryptography algorithms, such as Rivest–Shamir–Adleman (RSA). Google

YouTube disrupted in Pakistan as former…
Advertisement NetBlocks metrics confirm the disruption of YouTube on multiple internet providers in Pakistan on Sunday 21 August 2022. The disruption comes as former Prime Minister Imran Khan makes a live broadcast to the public, despite a ban issued by the Pakistan Electronic Media Regulatory Authority (PEMRA). Real-time network data show the disruption in effect