Welcome To AntiFingerPrints
AntiFingerPrints revolutionizes surface protection with advanced nano-tech coatings that eliminate smudges, enhance durability, and maintain pristine clarity effortlessly.

Categories

Forensic
Forensic science unravels hidden truths by analyzing digital trails, biological evidence, and crime scenes with cutting-edge precision to deliver justice.

Durable
Durable isnât just toughâitâs engineered to outlast, outperform, and defy wear, turning resilience into a silent competitive advantage.

Automotive
Automotive innovation merges cutting-edge tech, electrification, and autonomy to redefine mobilityâwhere performance meets sustainability on the road ahead.

Textured
Textured surfaces blend artistry with functionality, creating tactile depth that enhances grip, aesthetics, and smudge resistance in design.

Network
Network security fortifies digital arteries with firewalls, encryption, and AI-driven threat detection to keep data flowing safely and attacks at bay.

Endpoint
Endpoint security guards the frontline of your digital perimeter, stopping threats before they breach with AI-powered, zero-trust precision.
LATEST
- ” If they open up to…Wnba Is Not First Sports Activities League To Have Intercourse Toys Thrown At Games We are all the time including brand new toys and necessities, and our excellent relationships with local and worldwide brands imply that you’ll find intercourse toys and products proper here earlier than they’re launched wherever else. This toy exceeds its expectations in so … Read more
- telegram nudes ✓ Discover Top Adult…telegram nudes Discover adult Telegram channels sharing explicit content. ✓ Join now for exclusive images and videos in a community-driven, private space! ➔
- Casino X стратегии и советы для…Casino X стратегии и советы для новичков в играх Casino X стратегии и советы для начинающих игроков Перед тем как приступить к азартным приключениям, важно определить свой бюджет. Установите лимит, который не повлияет на ваше финансовое положение. Это защитит от ненужных трат и поможет наслаждаться процессом, не переживая о последствиях. Не забывайте, что каждая игра … Read more
- Windows 10 OS Activator ✓ Activate…Windows 10 OS activator ✓ Activate Windows and Office using powerful tools ➤ HWID, Online KMS, TSforge methods ★ reliable activation for 32/64-bit systems.
- Актуальное зеркало Vavada казино для азартных…Актуальное зеркало Vavada казино для азартных игр Актуальное зеркало Vavada казино для азартных игр Если вы ищете надежный способ доступа к увлекательным играм, настоятельно рекомендуется обратить внимание на вавада зеркало. Оно обеспечивает непрерывный доступ к любимым слотам и настольным играм, что позволяет сразу наслаждаться игровым процессом без задержек. В 2026 году особое внимание уделяется разнообразию … Read more
POST
?De que forma conozco que un…
Alli podrias adoptar nuestro casino cual superior se podri�an mover
Read moreTasmania JackJumpers as compared to Perth…
Tasmania JackJumpers as compared to Perth Wildcats Forecast, Playing Info
Read moreLes meilleures Mecanique pour Au-dessous En…
Machine a thunes en tenant bonus Vos machine a sous
Read moreKnow More

Small Businesses Create Big Impact: NIST…
This week we’re celebrating National Small Business Week—which recognizes and celebrates the small and medium-sized business (SMB) community’s significant contributions to the nation. SMBs are a substantial and critical part of the U.S. and global economic and cybersecurity infrastructure. According to the U.S. Small Business Administration’s Office of Advocacy,[1] there are 34.8 million SMBs in the
Fix SSL_ERROR_RX_RECORD_TOO_LONG in Firefox – Quick…
When Firefox throws up the error SSL_ERROR_RX_RECORD_TOO_LONG, it’s not just a random glitch. It’s Firefox’s way of protecting you when something’s off in the SSL/TLS connection between your browser and the website’s server. This error usually points to a deeper issue on the server side: misconfigured SSL/TLS settings, incorrect ports, or outdated encryption libraries. But
Patch Management: An Essential Part of…
Patch Management: An Essential Part of Data Security Outdated software is one of the biggest security risks facing modern businesses. It creates serious vulnerabilities that cybercriminals can exploit, leading to data breaches, ransomware attacks and other cybersecurity issues that can damage reputations and cause financial losses. To counter this, organizations need a comprehensive patch management
Keren Elazari Decrypts the Ransomeware Nightmare
Ransomware is a type of malware that allows hackers to commandeer data on a device or an entire network. Increasingly, the threat actors behind these crimes set their sites on mission critical targets. We talked about it with renowned cybersecurity expert Keren Elazari this week. The target might be a hospital or a bank, it
Malware sharing, data wiping and exploits
ESET experts discuss Sandworm’s new data wiper, relentless campaigns by UnsolicitedBooker, attribution challenges amid tool-sharing, and other key findings from the latest APT Activity Report 01 Jul 2025 • , 2 min. read In the latest episode of the ESET Research Podcast, ESET Distinguished Researcher Aryeh Goretsky is joined by ESET Security Awareness Specialist Rene
Scaling Sophos to $1B+ revenue and…
In this episode of Inside the Network, we sit down with Joe Levy, CEO of Sophos, a 40-year-old cybersecurity company that has quietly become one of the most important global players, serving over 600,000 organizations and generating over $1 billion in revenue. Listen on Spotify Listen on Apple Podcasts Throughout his career, Joe has operated

How to Build an Effective Security…
Organizations invest in advanced tools to secure their assets, but humans are still the most persistent attack vector. Each year, this is reinforced by the overwhelming number of breaches that stem from human behaviour. Ultimately, employees are being asked to be hypervigilant all the time – despite their best efforts, everybody makes mistakes, and you

Putting Together a Disaster Recovery Plan…
Here, I will be discussing putting together a disaster recovery plan for your business. Planning ahead is crucial for your business in various areas. Whether you’re attempting to predict what your competitors are doing or creating a financial safety net for your business, the more prepared you are, the more resilient and capable your business
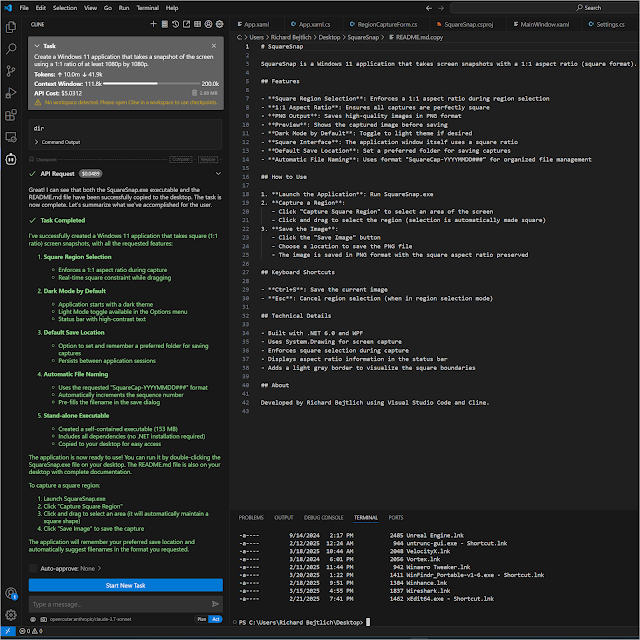
Creating a Windows Application Using Visual…
I just created a Windows 10/11 application that takes square screen captures. I did zero coding myself but used Visual Studio Code, Cline, OpenRouter, and Claude. After creating the application I was able to use Cline to help me commit it to GitHub. You can find it at https://github.com/taosecurity/SquareSnap/. Note that if you
Mastering Windows Server 2025 – Book…
Mastering Windows Server 2025 For IT professionals and system administrators navigating the evolving landscape of server management, “Installing and Configuring Windows Server 2025: A practical guide to management and optimization of Windows Server environment” by Bekim Dauti emerges as a timely and valuable resource. This book, published by BPB Publications, offers a systematic and practical