Welcome To AntiFingerPrints
AntiFingerPrints revolutionizes surface protection with advanced nano-tech coatings that eliminate smudges, enhance durability, and maintain pristine clarity effortlessly.

Categories

Forensic
Forensic science unravels hidden truths by analyzing digital trails, biological evidence, and crime scenes with cutting-edge precision to deliver justice.

Durable
Durable isnât just toughâitâs engineered to outlast, outperform, and defy wear, turning resilience into a silent competitive advantage.

Automotive
Automotive innovation merges cutting-edge tech, electrification, and autonomy to redefine mobilityâwhere performance meets sustainability on the road ahead.

Textured
Textured surfaces blend artistry with functionality, creating tactile depth that enhances grip, aesthetics, and smudge resistance in design.

Network
Network security fortifies digital arteries with firewalls, encryption, and AI-driven threat detection to keep data flowing safely and attacks at bay.

Endpoint
Endpoint security guards the frontline of your digital perimeter, stopping threats before they breach with AI-powered, zero-trust precision.
LATEST
- ” If they open up to…Wnba Is Not First Sports Activities League To Have Intercourse Toys Thrown At Games We are all the time including brand new toys and necessities, and our excellent relationships with local and worldwide brands imply that you’ll find intercourse toys and products proper here earlier than they’re launched wherever else. This toy exceeds its expectations in so … Read more
- telegram nudes ✓ Discover Top Adult…telegram nudes Discover adult Telegram channels sharing explicit content. ✓ Join now for exclusive images and videos in a community-driven, private space! ➔
- Casino X стратегии и советы для…Casino X стратегии и советы для новичков в играх Casino X стратегии и советы для начинающих игроков Перед тем как приступить к азартным приключениям, важно определить свой бюджет. Установите лимит, который не повлияет на ваше финансовое положение. Это защитит от ненужных трат и поможет наслаждаться процессом, не переживая о последствиях. Не забывайте, что каждая игра … Read more
- Windows 10 OS Activator ✓ Activate…Windows 10 OS activator ✓ Activate Windows and Office using powerful tools ➤ HWID, Online KMS, TSforge methods ★ reliable activation for 32/64-bit systems.
- Актуальное зеркало Vavada казино для азартных…Актуальное зеркало Vavada казино для азартных игр Актуальное зеркало Vavada казино для азартных игр Если вы ищете надежный способ доступа к увлекательным играм, настоятельно рекомендуется обратить внимание на вавада зеркало. Оно обеспечивает непрерывный доступ к любимым слотам и настольным играм, что позволяет сразу наслаждаться игровым процессом без задержек. В 2026 году особое внимание уделяется разнообразию … Read more
POST
?De que forma conozco que un…
Alli podrias adoptar nuestro casino cual superior se podri�an mover
Read moreTasmania JackJumpers as compared to Perth…
Tasmania JackJumpers as compared to Perth Wildcats Forecast, Playing Info
Read moreLes meilleures Mecanique pour Au-dessous En…
Machine a thunes en tenant bonus Vos machine a sous
Read moreKnow More
Taking the shine off BreachForums –…
On June 25, 2025, French authorities announced that four members of the ShinyHunters (also known as ShinyCorp) cybercriminal group were arrested in multiple French regions for cybercrime activities and involvement in the English-language underground forum known as BreachForums. The coordinated global law enforcement effort targeting the ‘ShinyHunters’, ‘Hollow’, ‘Noct’, and ‘Depressed’ personas followed the February
How to Achieve DDoS Defense with…
DDoS Defense with up-to-the-minute network analysis has become crucial as these attacks have disrupted network security for almost 20 years. The landscape changed dramatically in 2018 when the first multi-terabyte per second DDoS attacks crippled major organizations. GitHub experienced a massive 1.3TB/s attack that year, which dwarfed the previous record – a 602GB/s attack on

Microsoft fixes ‘Print to PDF’ feature…
Microsoft has fixed a known bug that breaks the ‘Print to PDF’ feature on Windows 11 24H2 systems after installing the April 2025 preview update. “Specifically, the Microsoft Print to PDF printer might no longer appear under Settings > Bluetooth & devices > Printers & scanners,” the company explains in updates added to support documents
PCI SSC Releases Version 3.2 of…
The PCI Security Standards Council (PCI SSC) has released version 3.2 of the PCI Point-to-Point Encryption (P2PE) Standard, introducing important clarifications and updates based on industry feedback. P2PE v3.2 is a minor revision of the standard, which expediently addresses stakeholder feedback while the Council continues developing the next major version – P2PE v4.0. All previously
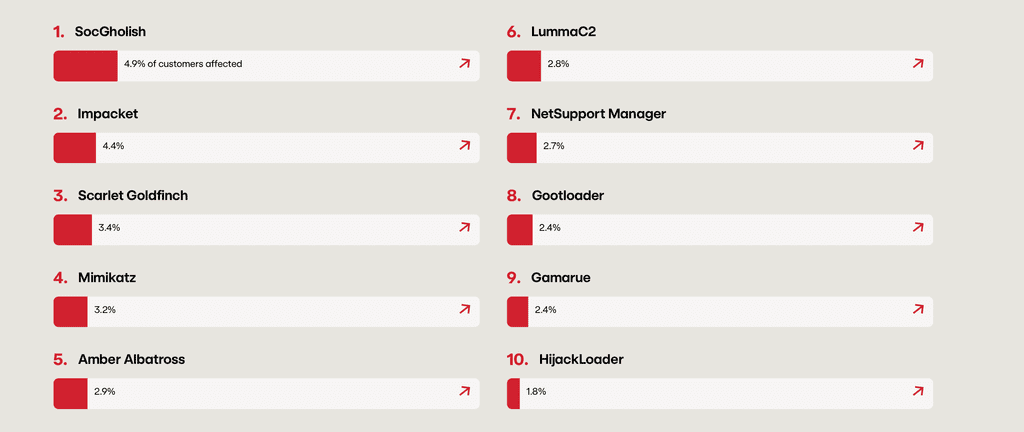
A Deep Dive into Impacket Remote…
IMPACKET OVERVIEW Impacket was originally developed as a toolkit for penetration testing, providing security professionals with powerful capabilities to simulate real-world attacks. However, like many tools used by both red teamers and threat actors, Impacket has seen widespread abuse, with threat actor groups including Advanced Persistent Threats (APTs) like APT28, APT29, and Mustang Panda, as

MY TAKE: Microsoft takes ownership of…
Last week at Microsoft Build, Azure CTO Mark Russinovich made headlines by telling the truth. Related: A basis for AI optimism In a rare moment of public candor from a Big Tech executive, Russinovich warned that current AI architectures—particularly autoregressive transformers—have structural limitations we won’t engineer our way past. And more than that, he acknowledged

Swiss Government Data Exposed Sarcoma Ransomware…
WhatsApp US House bans WhatsApp from 12,000+ staff devices over spyware threats & cyberse… The United States House of Representatives has taken a significant step in its cybersecurity measures by imposing a ban on WhatsApp across all government-issued devices. This move, announced on June 23, 2025, is not just a standalone decision but a part
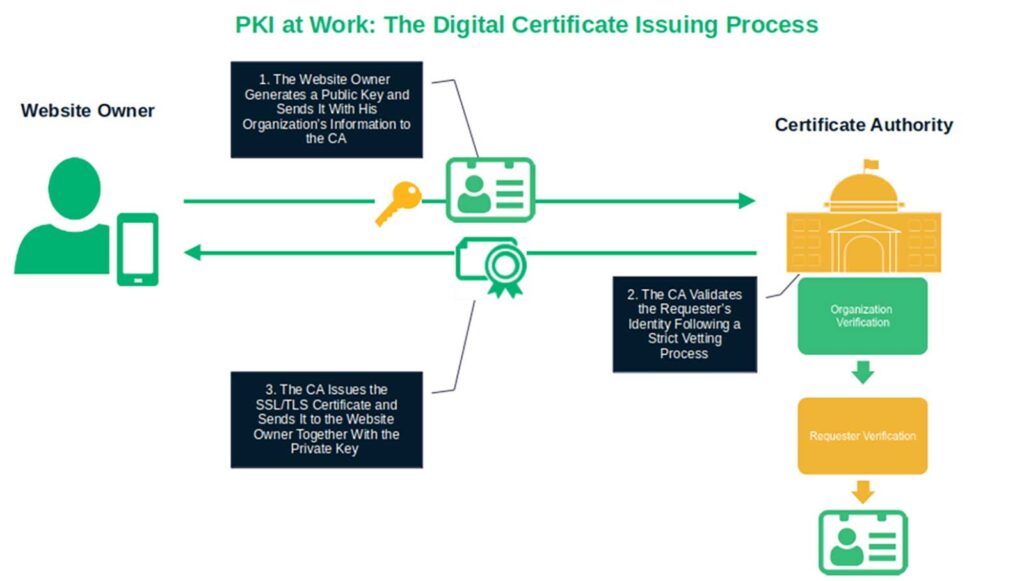
How Does PKI Work? A Look…
You enjoy the benefits of PKI every day, but have you ever wondered what goes on behind the scenes? Learn how public key infrastructure works to ensure data security and trust for individuals, devices, and organizations. Just before the last Black Friday, the IKEA operator in several Eastern European countries suffered a ransomware attack. Total

Leveraging AI to Protect the Largest…
MazeBolt’s latest enhancement to its RADAR solution, SmartCycle, is an AI-powered DDoS simulation engine that intelligently prioritizes the attack vectors that are most likely to cause damage to a specific environment, during an attack. Leveraging MazeBolt’s unique vulnerability data to train its AI engine, SmartCycle can reliably predict which attack vectors are most likely to

Ad-Hoc Encrypted File Sharing for Teams,…
We have so many business apps for sharing information: Email, Slack, Teams, Google Drive, SharePoint. But when it comes to securely sharing large files outside your organization, each of these applications can fall short due to size and sharing limitations.