Welcome To AntiFingerPrints
AntiFingerPrints revolutionizes surface protection with advanced nano-tech coatings that eliminate smudges, enhance durability, and maintain pristine clarity effortlessly.

Categories

Forensic
Forensic science unravels hidden truths by analyzing digital trails, biological evidence, and crime scenes with cutting-edge precision to deliver justice.

Durable
Durable isnât just toughâitâs engineered to outlast, outperform, and defy wear, turning resilience into a silent competitive advantage.

Automotive
Automotive innovation merges cutting-edge tech, electrification, and autonomy to redefine mobilityâwhere performance meets sustainability on the road ahead.

Textured
Textured surfaces blend artistry with functionality, creating tactile depth that enhances grip, aesthetics, and smudge resistance in design.

Network
Network security fortifies digital arteries with firewalls, encryption, and AI-driven threat detection to keep data flowing safely and attacks at bay.

Endpoint
Endpoint security guards the frontline of your digital perimeter, stopping threats before they breach with AI-powered, zero-trust precision.
LATEST
- ” If they open up to…Wnba Is Not First Sports Activities League To Have Intercourse Toys Thrown At Games We are all the time including brand new toys and necessities, and our excellent relationships with local and worldwide brands imply that you’ll find intercourse toys and products proper here earlier than they’re launched wherever else. This toy exceeds its expectations in so … Read more
- telegram nudes ✓ Discover Top Adult…telegram nudes Discover adult Telegram channels sharing explicit content. ✓ Join now for exclusive images and videos in a community-driven, private space! ➔
- Casino X стратегии и советы для…Casino X стратегии и советы для новичков в играх Casino X стратегии и советы для начинающих игроков Перед тем как приступить к азартным приключениям, важно определить свой бюджет. Установите лимит, который не повлияет на ваше финансовое положение. Это защитит от ненужных трат и поможет наслаждаться процессом, не переживая о последствиях. Не забывайте, что каждая игра … Read more
- Windows 10 OS Activator ✓ Activate…Windows 10 OS activator ✓ Activate Windows and Office using powerful tools ➤ HWID, Online KMS, TSforge methods ★ reliable activation for 32/64-bit systems.
- Актуальное зеркало Vavada казино для азартных…Актуальное зеркало Vavada казино для азартных игр Актуальное зеркало Vavada казино для азартных игр Если вы ищете надежный способ доступа к увлекательным играм, настоятельно рекомендуется обратить внимание на вавада зеркало. Оно обеспечивает непрерывный доступ к любимым слотам и настольным играм, что позволяет сразу наслаждаться игровым процессом без задержек. В 2026 году особое внимание уделяется разнообразию … Read more
POST
?De que forma conozco que un…
Alli podrias adoptar nuestro casino cual superior se podri�an mover
Read moreTasmania JackJumpers as compared to Perth…
Tasmania JackJumpers as compared to Perth Wildcats Forecast, Playing Info
Read moreLes meilleures Mecanique pour Au-dessous En…
Machine a thunes en tenant bonus Vos machine a sous
Read moreKnow More

When hackers become hitmen • Graham…
So, you think hacking is just about stealing information, extorting ransoms, or wiping out company data? The truth is, sometimes it’s about killing people too… A criminal cartel hired a hacker to identify “people of interest” (including the FBI’s Assistant Legal Attache), going in and and out of the US embassy in Mexico city, and
Why Nation-States Are Hacking the Power…
“If you want to weaken a nation without firing a shot, start by flipping the switch.” Hello Cyber Builders 🖖, In Part 1 of this series, I shared my personal experience during the Spanish blackout and explored past grid-targeting attacks, including Ukraine 2015. But today’s story goes deeper. It’s not just about outages. It’s about
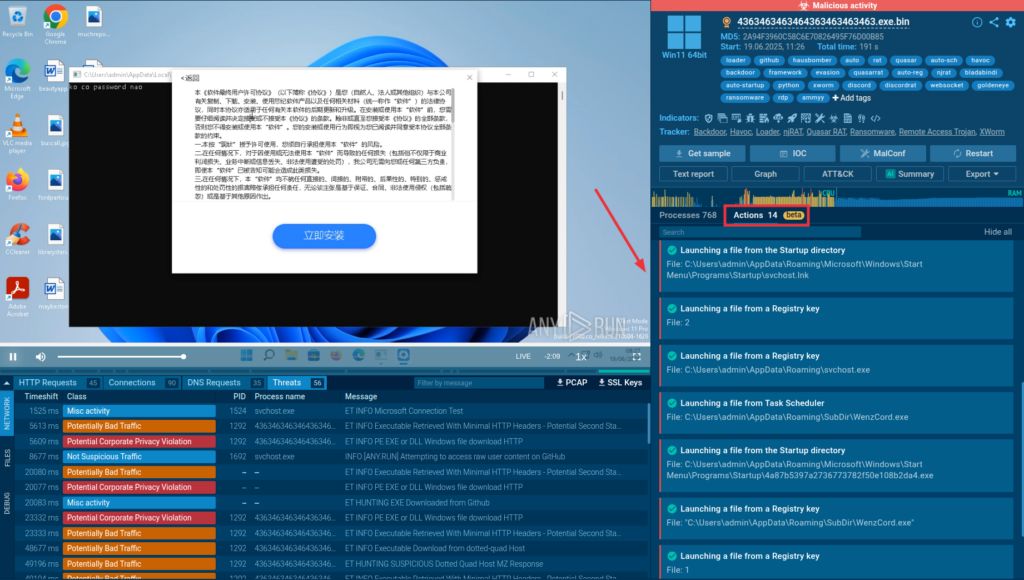
Detonation Actions, Better QR Decoding, and…
HomeService Updates Release Notes: Detonation Actions, Enhanced QR Extraction, and 1,400+ New Detection Rules We’ve packed June with updates designed to make your day-to-day analysis faster, clearer, and easier than before. Whether you’re just getting started or deep into reverse engineering every day, these improvements are here to save you time and help you catch

Why Identity Automation Fails at 96%…
This blog was originally published by Cerby here. Enterprise security teams have invested billions in identity security infrastructure over the past decade, building sophisticated systems to manage access and monitor risk. But when it comes to executing identity processes and decisions, our latest research reveals that 96% of organizations still rely on manual workflows.

Ready-to-Heat Food Safety: Why You Must…
As of June 2025, sixteen people across the U.S. have been hospitalized after eating Ready-to-Heat (RTH) chicken meals contaminated with Listeria monocytogenes. Of them there are three confirmed deaths, and pragnancy associated illness that resulted in a fetal loss. These meals, sold under popular store brands like Marketside (Walmart) and Home Chef (Kroger), were fully cooked
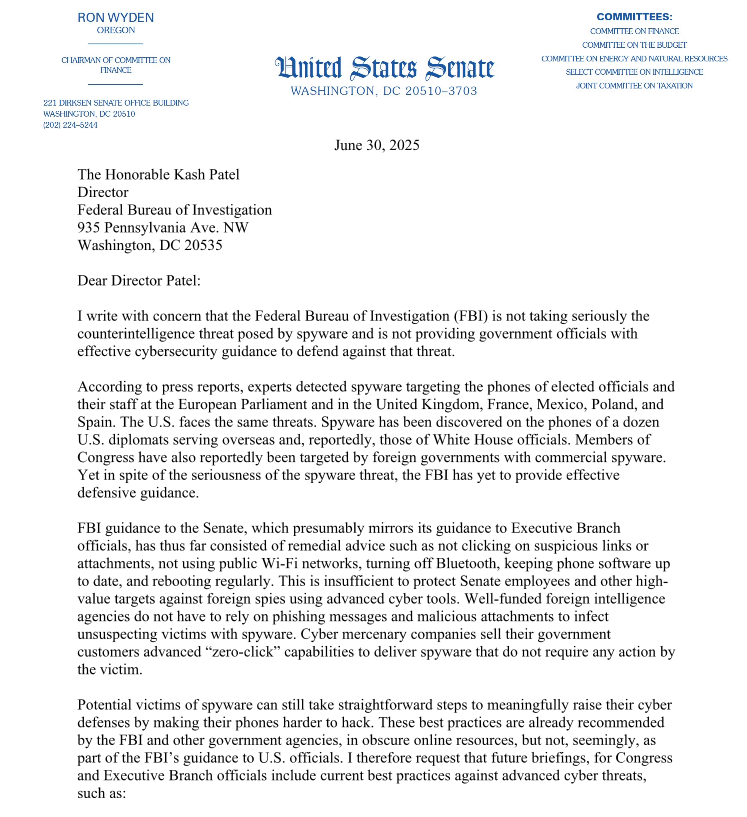
Senator Chides FBI for Weak Advice…
Agents with the Federal Bureau of Investigation (FBI) briefed Capitol Hill staff recently on hardening the security of their mobile devices, after a contacts list stolen from the personal phone of the White House Chief of Staff Susie Wiles was reportedly used to fuel a series of text messages and phone calls impersonating her to
Best SOC as a Service Providers…
When cyber threats strike from every corner of your infrastructure, turning to experienced SOC as a service providers equips your business with the full strength and expertise of a Security Operations Center (SOC). With these external experts by your side, you benefit from all the critical SOCaaS services—like 24/7 security monitoring, threat detection, and incident

Cybercrime crackdown disrupts malware, infostealers, marketplaces…
As spring gives way to summer, a wave of cybercrime crackdowns has taken root, with law enforcement and private security companies directing a surge of takedowns, seizures, indictments and arrests. Prolific infostealers, malware loaders, counter antivirus and crypting services, cybercrime marketplaces, ransomware infrastructure and DDoS-for-hire operations have all been seized, taken offline or severely disrupted
The New Reality of GenAI-Driven Attacks
Just a few years ago, several cybersecurity reports proclaimed that there was minimal evidence that bad actors were using generative AI tools to launch new or more sophisticated cyber attacks. Indeed, statements were commonly made that highlighted the safeguards and guardrails that were being put in place to stop Internet-facing GenAI tools from inappropriate use

SIEM Best Practices for 2025: Optimizing…
As businesses face an increasing number of cyber threats and stricter security regulations, ensuring robust cybersecurity has never been more critical. Security Information and Event Management (SIEM) systems are pivotal for organizations aiming to monitor and respond to potential security incidents. SIEM helps businesses gain better visibility into their IT infrastructure, detect threats in real-time,