Welcome To AntiFingerPrints
AntiFingerPrints revolutionizes surface protection with advanced nano-tech coatings that eliminate smudges, enhance durability, and maintain pristine clarity effortlessly.

Categories

Forensic
Forensic science unravels hidden truths by analyzing digital trails, biological evidence, and crime scenes with cutting-edge precision to deliver justice.

Durable
Durable isnât just toughâitâs engineered to outlast, outperform, and defy wear, turning resilience into a silent competitive advantage.

Automotive
Automotive innovation merges cutting-edge tech, electrification, and autonomy to redefine mobilityâwhere performance meets sustainability on the road ahead.

Textured
Textured surfaces blend artistry with functionality, creating tactile depth that enhances grip, aesthetics, and smudge resistance in design.

Network
Network security fortifies digital arteries with firewalls, encryption, and AI-driven threat detection to keep data flowing safely and attacks at bay.

Endpoint
Endpoint security guards the frontline of your digital perimeter, stopping threats before they breach with AI-powered, zero-trust precision.
LATEST
- ” If they open up to…Wnba Is Not First Sports Activities League To Have Intercourse Toys Thrown At Games We are all the time including brand new toys and necessities, and our excellent relationships with local and worldwide brands imply that you’ll find intercourse toys and products proper here earlier than they’re launched wherever else. This toy exceeds its expectations in so … Read more
- telegram nudes ✓ Discover Top Adult…telegram nudes Discover adult Telegram channels sharing explicit content. ✓ Join now for exclusive images and videos in a community-driven, private space! ➔
- Casino X стратегии и советы для…Casino X стратегии и советы для новичков в играх Casino X стратегии и советы для начинающих игроков Перед тем как приступить к азартным приключениям, важно определить свой бюджет. Установите лимит, который не повлияет на ваше финансовое положение. Это защитит от ненужных трат и поможет наслаждаться процессом, не переживая о последствиях. Не забывайте, что каждая игра … Read more
- Windows 10 OS Activator ✓ Activate…Windows 10 OS activator ✓ Activate Windows and Office using powerful tools ➤ HWID, Online KMS, TSforge methods ★ reliable activation for 32/64-bit systems.
- Актуальное зеркало Vavada казино для азартных…Актуальное зеркало Vavada казино для азартных игр Актуальное зеркало Vavada казино для азартных игр Если вы ищете надежный способ доступа к увлекательным играм, настоятельно рекомендуется обратить внимание на вавада зеркало. Оно обеспечивает непрерывный доступ к любимым слотам и настольным играм, что позволяет сразу наслаждаться игровым процессом без задержек. В 2026 году особое внимание уделяется разнообразию … Read more
POST
?De que forma conozco que un…
Alli podrias adoptar nuestro casino cual superior se podri�an mover
Read moreTasmania JackJumpers as compared to Perth…
Tasmania JackJumpers as compared to Perth Wildcats Forecast, Playing Info
Read moreLes meilleures Mecanique pour Au-dessous En…
Machine a thunes en tenant bonus Vos machine a sous
Read moreKnow More

Auf der Suche nach Alternativen zum…
Aktuelle Alternativen umfassen verschiedene Anbieterquellen Unabhängige Anbieter von aggregierten Schwachstelleninformationen wie Flashpoint, VulnCheck, Tenable, BitSight und andere sind eine weitere Option. „Viele dieser Anbieter bieten kuratierte Datensätze, die Schwachstellen erfassen, die von CVE oft übersehen oder verzögert gemeldet werden“, so Lefkowitz. „Sie bieten auch wichtige Kontextinformationen wie Ausnutzbarkeit, Ransomware-Risiko und soziales Risiko.“ Um diese Informationen

The Generative AI Revolution: Trends That…
The Generative AI Revolution: Trends That Will Shape Your 2025 Strategy Hey there, tech-savvy reader! Let’s admit it—Generative AI is no longer some futuristic buzzword floating around in TED Talks or sci-fi flicks. It’s here. It’s working. And it’s reshaping everything—from how we work, to how we create, to how we think. 2025 is turning

Cybersecurity Compliance in South Africa
A Continued Cycle South Africa has had a slow approach to compliance with the government regulations and laws set in place. This problem has been exposed at every turn as South Africa has continued to show its vulnerabilities, and cyber criminals see them and abuse them. The institution of much of the newer legislation has
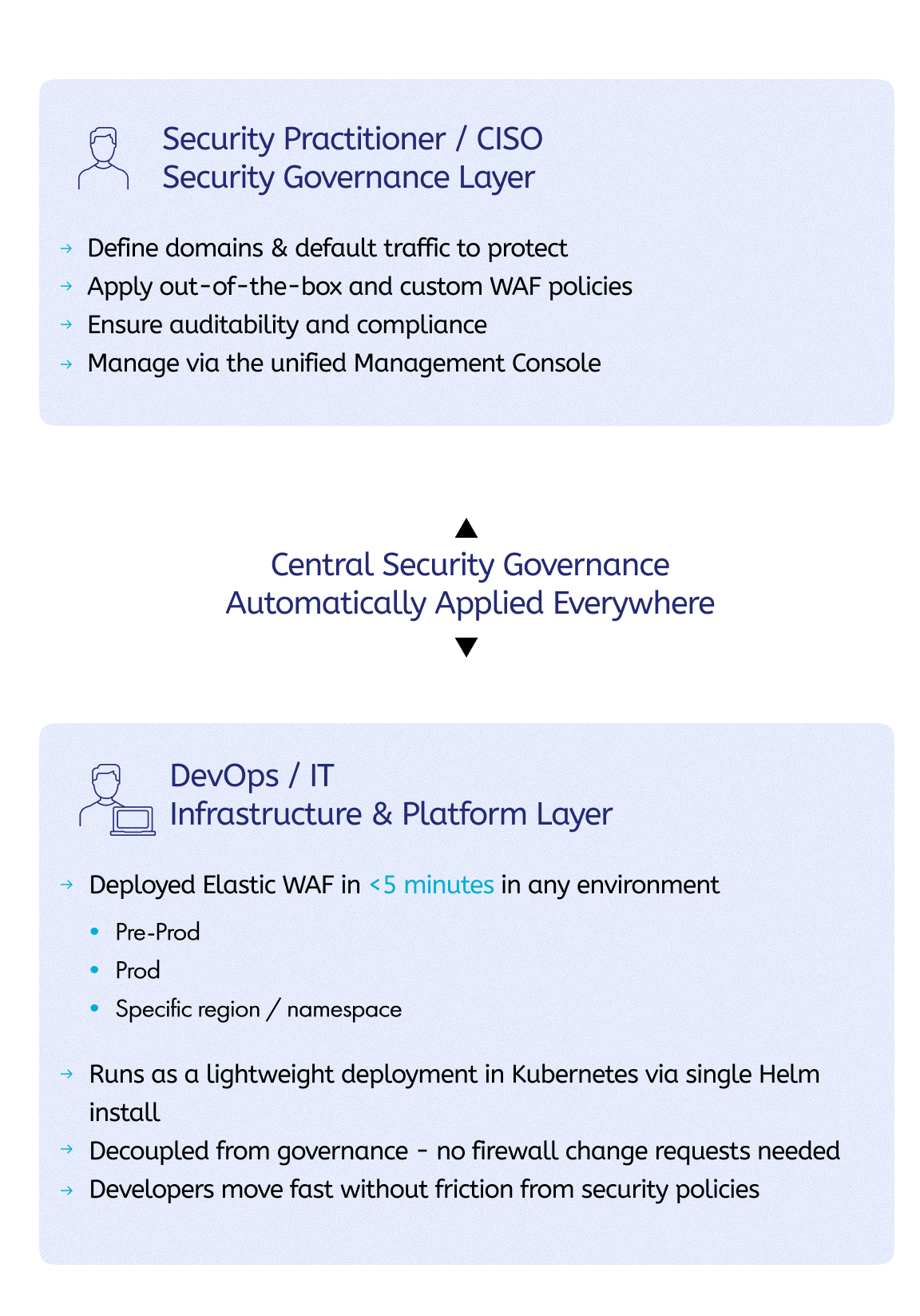
Elastic WAF: Reshaping Application Security for…
We recently discussed Imperva’s vision for the future of application security, where we also covered the Imperva Security Engine. This innovative application security framework is powering up the next generation of Imperva solutions, the first of which is Imperva Elastic WAF. This blog is the first in a series of deep-dive blogs into Elastic WAF.
Weekly Update 458
I'm in Austria! Well, I was in Austria, I'm now somewhere over the Aussie desert as I try and end this trip on top of my "to-do" list. The Have I Been Pwned Alpine Grand Tour was a great success with loads of time spent with govs, public meetups and users of this little data
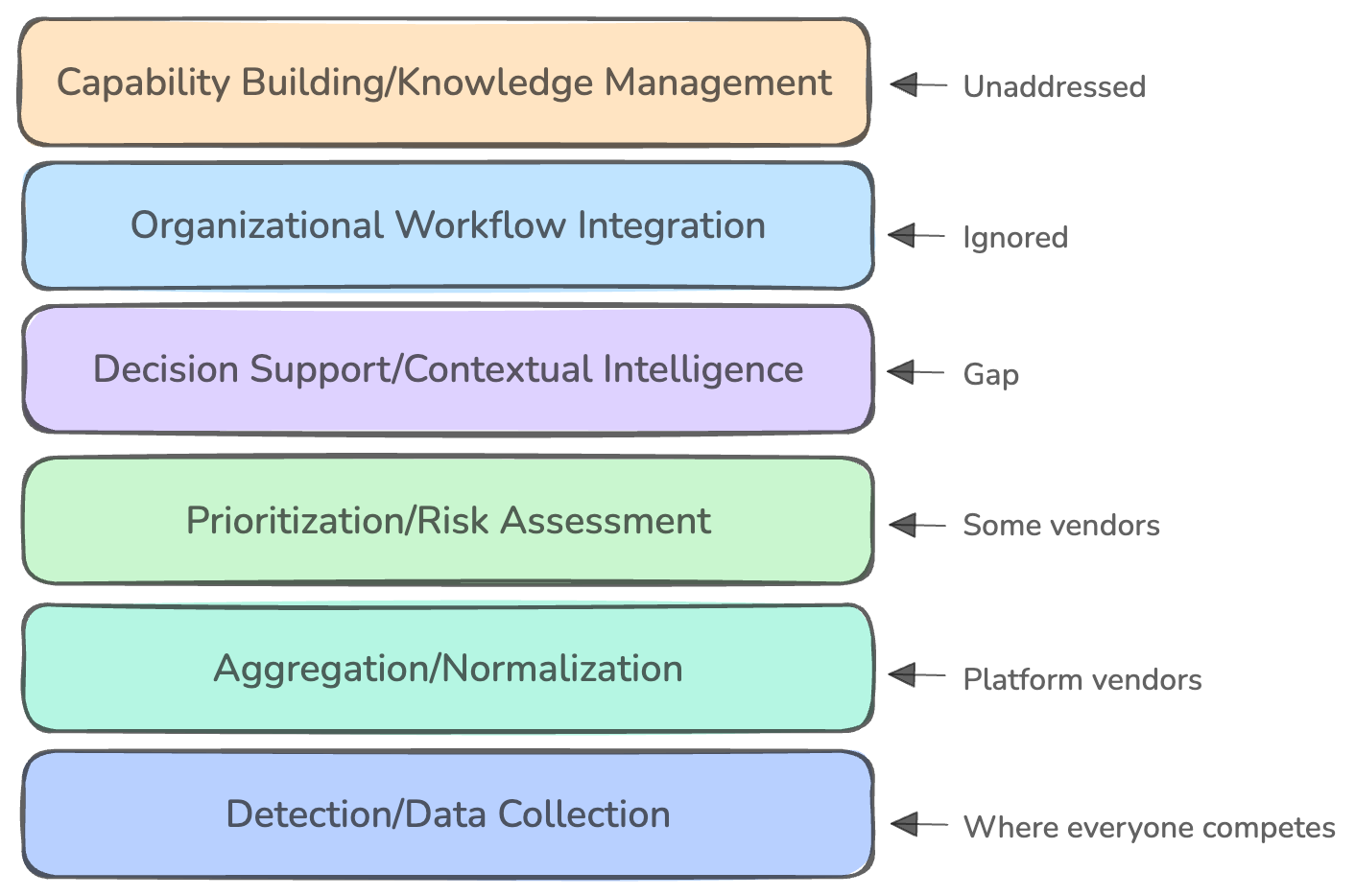
why theory doesn’t match practice
This week, Venture in Security is excited to feature a guest article from Nielet D’Mello. Nielet is a security engineer with nearly a decade of experience designing and scaling secure systems across the software development lifecycle. She has held roles at McAfee, Intel, and currently Datadog, working across consumer, enterprise, and cloud-native security domains. Her
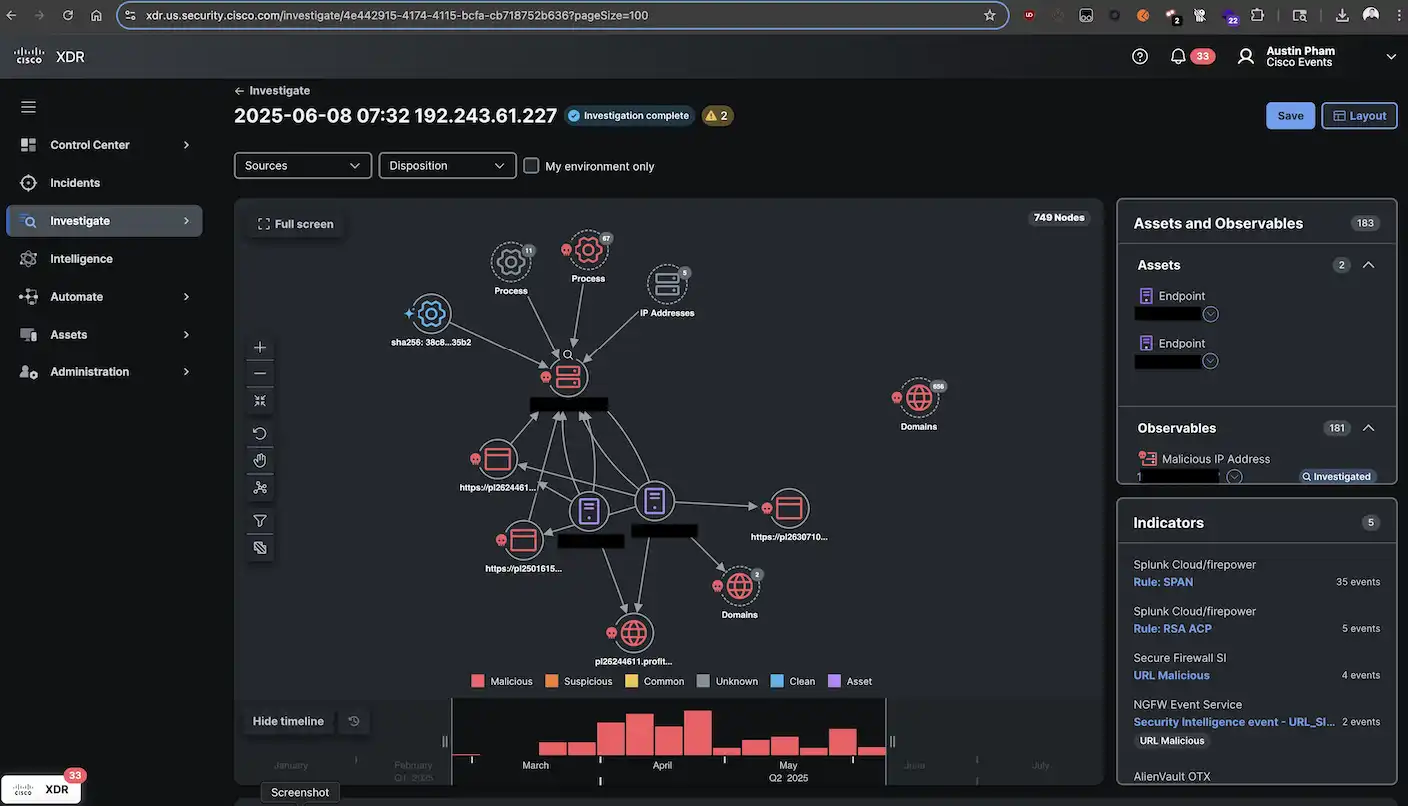
Splunk in Action at the Cisco…
Additional Post Contributors: Austin Pham, Tony Iacobelli Cisco and Splunk, together, elevate the SOC’s Incident Detection and Response experience to the next level by combining technologies from both sides that provide an even greater single pane of glass view to threats in real time. Technologies such as Cisco XDR and Security Cloud and Splunk Enterprise
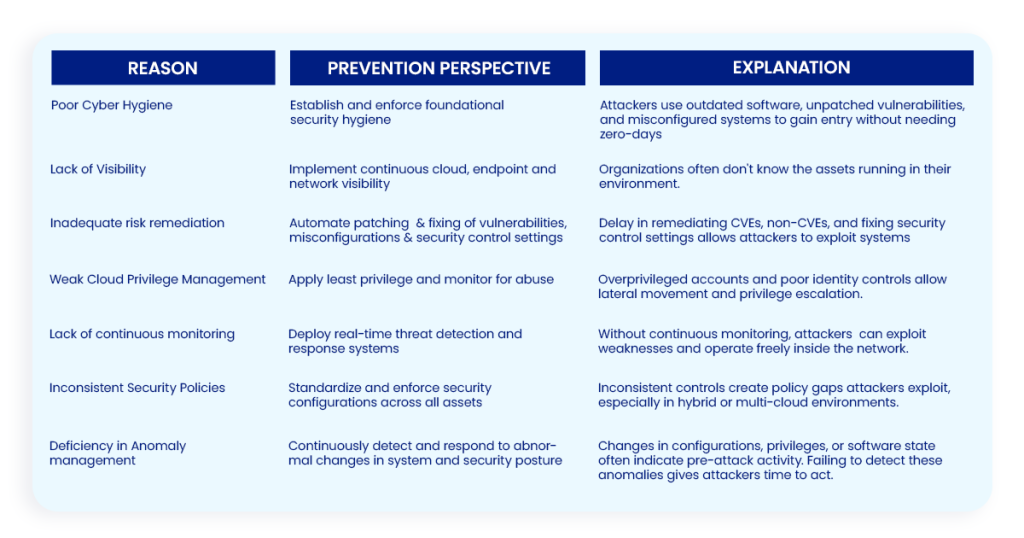
Proactive Cybersecurity: How to Prevent Cyber…
As we have seen, cyber-attacks can be highly damaging and disruptive. With their insatiable desire to gain power and dominance, attackers can unleash their intent in a stealthy and subtle manner to achieve their goals with precisely targeted and calibrated campaigns on a scale. These can be multi-stage theatre-level attacks (e.g., Stuxnet/Operation Aurora/Operation Cloud Hopper)
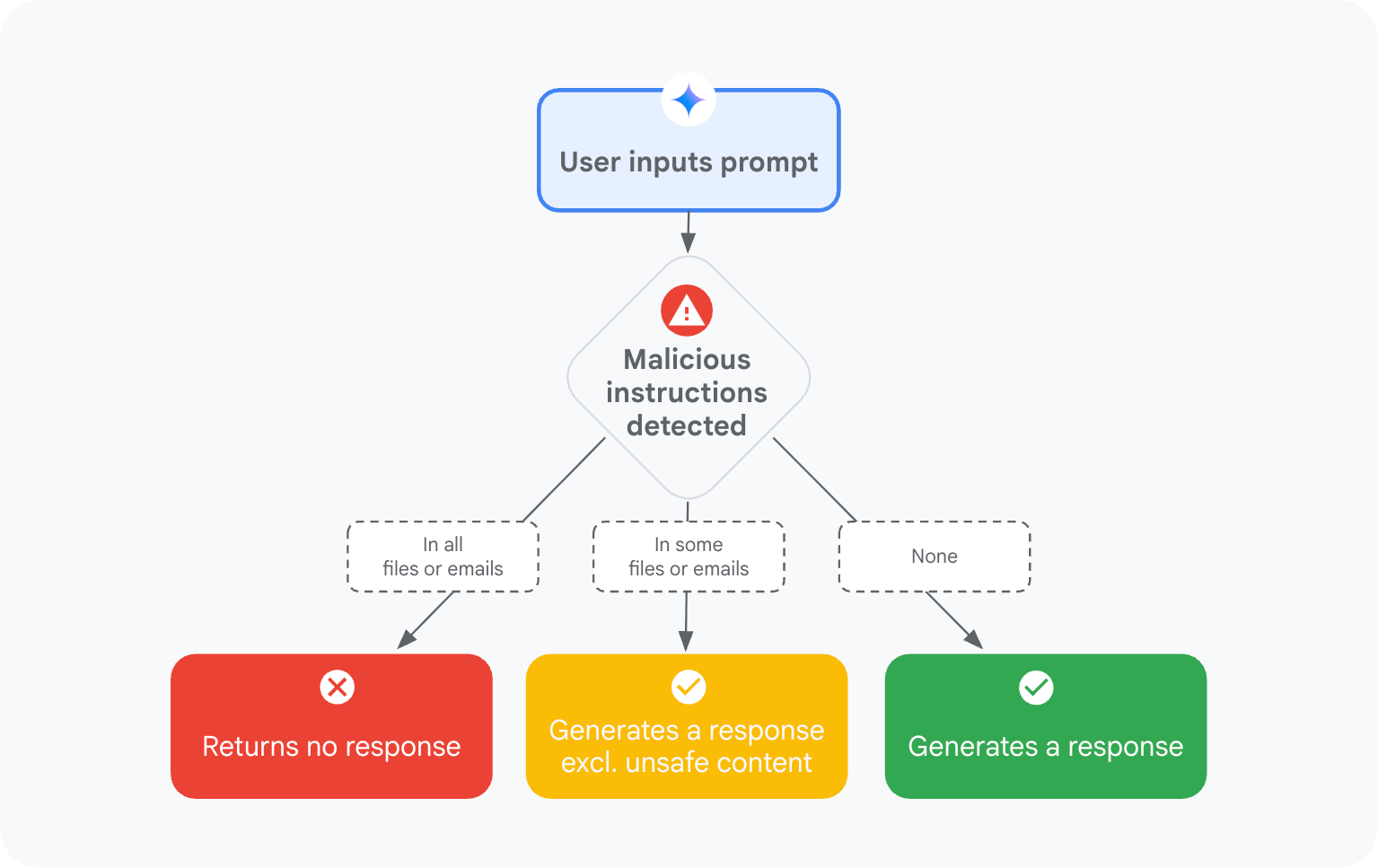
Mitigating prompt injection attacks with a…
With the rapid adoption of generative AI, a new wave of threats is emerging across the industry with the aim of manipulating the AI systems themselves. One such emerging attack vector is indirect prompt injections. Unlike direct prompt injections, where an attacker directly inputs malicious commands into a prompt, indirect prompt injections involve hidden malicious
Why Most Privacy Programs Fail Audits…
In privacy, what you don’t know can hurt you. Your Records of Processing Activities (ROPA) may be up to date. Your data flows may look airtight. But if your privacy team doesn’t have visibility into all the personal data processed in your organization—including the documents, emails, images and forgotten folders —then your program is built