Welcome To AntiFingerPrints
AntiFingerPrints revolutionizes surface protection with advanced nano-tech coatings that eliminate smudges, enhance durability, and maintain pristine clarity effortlessly.

Categories

Forensic
Forensic science unravels hidden truths by analyzing digital trails, biological evidence, and crime scenes with cutting-edge precision to deliver justice.

Durable
Durable isnât just toughâitâs engineered to outlast, outperform, and defy wear, turning resilience into a silent competitive advantage.

Automotive
Automotive innovation merges cutting-edge tech, electrification, and autonomy to redefine mobilityâwhere performance meets sustainability on the road ahead.

Textured
Textured surfaces blend artistry with functionality, creating tactile depth that enhances grip, aesthetics, and smudge resistance in design.

Network
Network security fortifies digital arteries with firewalls, encryption, and AI-driven threat detection to keep data flowing safely and attacks at bay.

Endpoint
Endpoint security guards the frontline of your digital perimeter, stopping threats before they breach with AI-powered, zero-trust precision.
LATEST
- ” If they open up to…Wnba Is Not First Sports Activities League To Have Intercourse Toys Thrown At Games We are all the time including brand new toys and necessities, and our excellent relationships with local and worldwide brands imply that you’ll find intercourse toys and products proper here earlier than they’re launched wherever else. This toy exceeds its expectations in so … Read more
- telegram nudes ✓ Discover Top Adult…telegram nudes Discover adult Telegram channels sharing explicit content. ✓ Join now for exclusive images and videos in a community-driven, private space! ➔
- Casino X стратегии и советы для…Casino X стратегии и советы для новичков в играх Casino X стратегии и советы для начинающих игроков Перед тем как приступить к азартным приключениям, важно определить свой бюджет. Установите лимит, который не повлияет на ваше финансовое положение. Это защитит от ненужных трат и поможет наслаждаться процессом, не переживая о последствиях. Не забывайте, что каждая игра … Read more
- Windows 10 OS Activator ✓ Activate…Windows 10 OS activator ✓ Activate Windows and Office using powerful tools ➤ HWID, Online KMS, TSforge methods ★ reliable activation for 32/64-bit systems.
- Актуальное зеркало Vavada казино для азартных…Актуальное зеркало Vavada казино для азартных игр Актуальное зеркало Vavada казино для азартных игр Если вы ищете надежный способ доступа к увлекательным играм, настоятельно рекомендуется обратить внимание на вавада зеркало. Оно обеспечивает непрерывный доступ к любимым слотам и настольным играм, что позволяет сразу наслаждаться игровым процессом без задержек. В 2026 году особое внимание уделяется разнообразию … Read more
POST
?De que forma conozco que un…
Alli podrias adoptar nuestro casino cual superior se podri�an mover
Read moreTasmania JackJumpers as compared to Perth…
Tasmania JackJumpers as compared to Perth Wildcats Forecast, Playing Info
Read moreLes meilleures Mecanique pour Au-dessous En…
Machine a thunes en tenant bonus Vos machine a sous
Read moreKnow More

Enhancing Endpoint Visibility Through a Unified…
It’s easy to miss critical signs when endpoint tools work in isolation. When a laptop shows unusual behavior but its network or cloud interactions are invisible, early compromise can go undetected. By bringing together endpoint detection and response (EDR), network telemetry, and cloud context under a unified security approach, teams gain the full picture needed
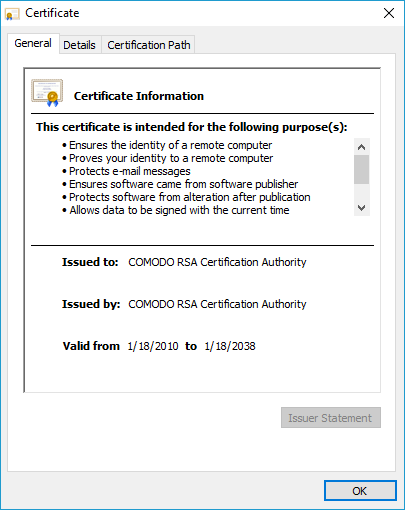
Comodo RSA Certification Authority: Trusted Root…
The COMODO RSA Certification Authority is one of the most widely distributed root CAs in the world. Its certificates form the foundation of security for millions of websites, applications, and digital services. But what makes COMODO RSA Certification Authority one of the most trusted names in web security? Let’s explore. Overview of Comodo RSA Certification

Microsegmentation: Strengthening Network Security Against Zero…
Microsegmentation: Strengthening Network Security Against Zero Day Exploits The challenge of how businesses respond to an ever-evolving cybersecurity landscape is a complex one. Threats like zero day exploits make it easier for cybercriminals to breach defenses and access sensitive data, leading to costly ransomware incidents. These vulnerabilities are especially hard to manage as networks expand

HOW TO BECOME CERTIFIED LEAD IMPLEMENTER…
Advertisement ABOUT CERTIFIED LEAD IMPLEMENTER TRAINING AND EXAMINATION FOR INFORMATION SECURITY MANAGEMENT SYSTEM ISO / IEC 27001 Learn and get certified as a professional in implementation of ISO 27001 standard through our self-paced E-learning interactive course which comprises of 4 modules. Upon completion of these modules, you can appear for an examination and get certified
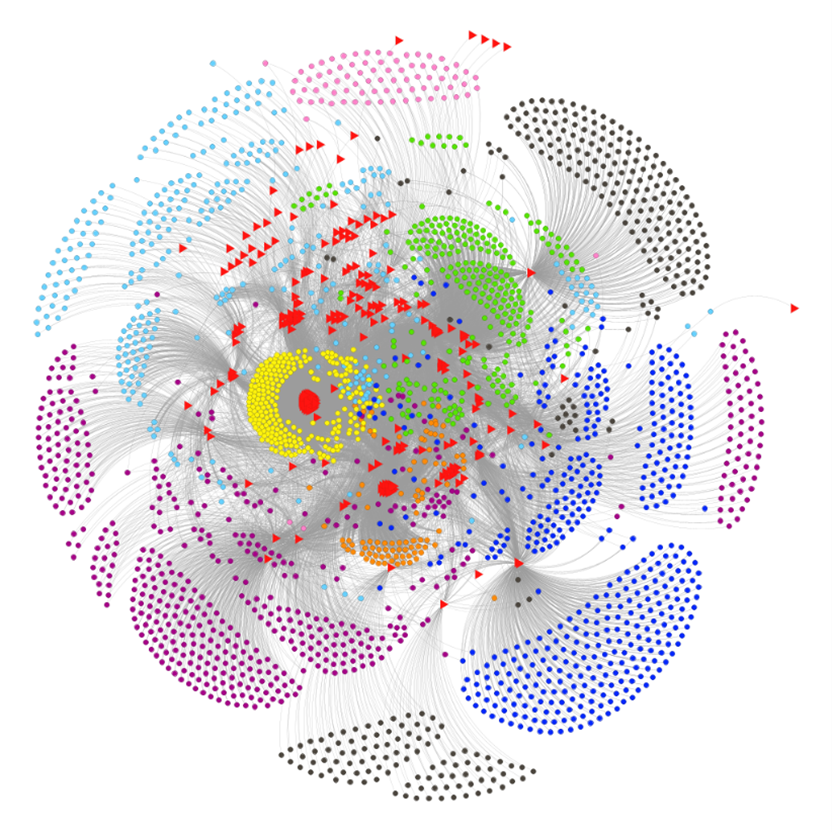
Using AI to identify cybercrime masterminds…
Online criminal forums, both on the public internet and on the “dark web” of Tor .onion sites, are a rich resource for threat intelligence researchers. The Sophos Counter Threat Unit (CTU) have a team of darkweb researchers collecting intelligence and interacting with darkweb forums, but combing through these posts is a time-consuming and resource-intensive task,

The Impact of Artificial Intelligence on…
Credit: NICE The NICE Workforce Framework for Cybersecurity (NICE Framework) was revised in November 2020 as NIST Special Publication 800-181 rev.1 to enable more effective and rapid updates to the NICE Framework Components, including how the advent of emerging technologies would impact cybersecurity work. NICE has been actively engaging in conversations with: federal departments and

India’s First Global Computer Virus
In the cinematic tapestry of cybersecurity, where tales of intrigue and innovation collide, one story emerges from the shadows of the past. It’s a story that began in the early 1990s, during the DOS era, when computer viruses were still a novel and mysterious menace. This is the tale of Joshi, a virus of Indian
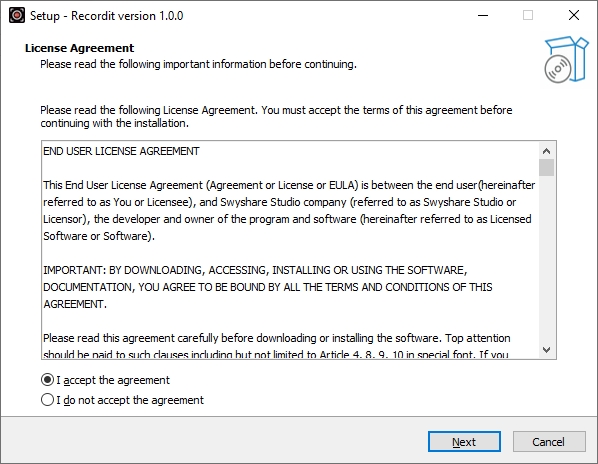
How To Record Your Screen Securely…
Learn how to record your screen securely with Recordit in this post. Screen recording has become an essential tool for professionals, educators, developers, and support teams. Whether you’re creating a software demo, reporting a bug, or recording a walkthrough for a colleague, screen recording offers a fast, visual way to communicate. However, recording and sharing
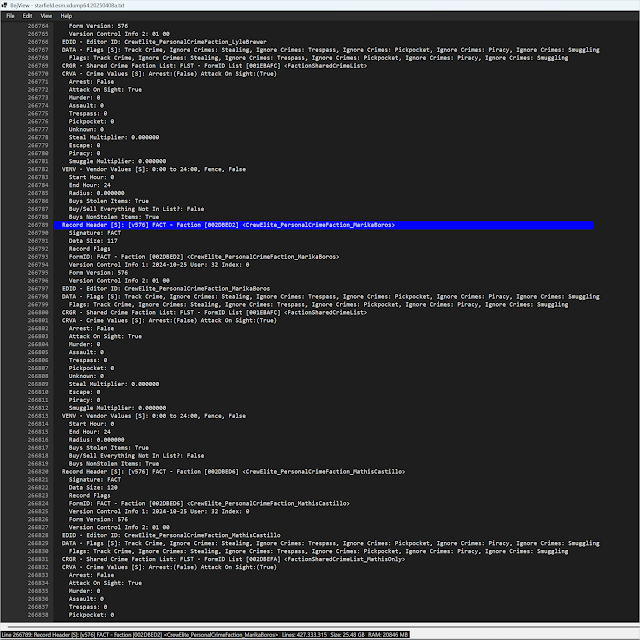
Creating a Large Text File Viewer…
The problem I was trying to solve this time was opening and searching extremely large text files. I used to use the old Mandiant Highlighter program for this, but it was last updated in 2011 and couldn’t handle the 26 GB text file I wanted to open. If you’re wondering what that
Shannon Edwards Reveals the Student Data…
As technology is integrated deeper into classrooms, the lines between education and data privacy have been destroyed by for-profit data miners. This week, privacy advocate Shannon Edwards reveals how educational apps harvest sensitive information from children, commodify their data, and what parents can do to fight it.